Vibe Coding Security Governance: How to Safely Adopt Codex, Claude Code, Cursor, and AI Coding Agents
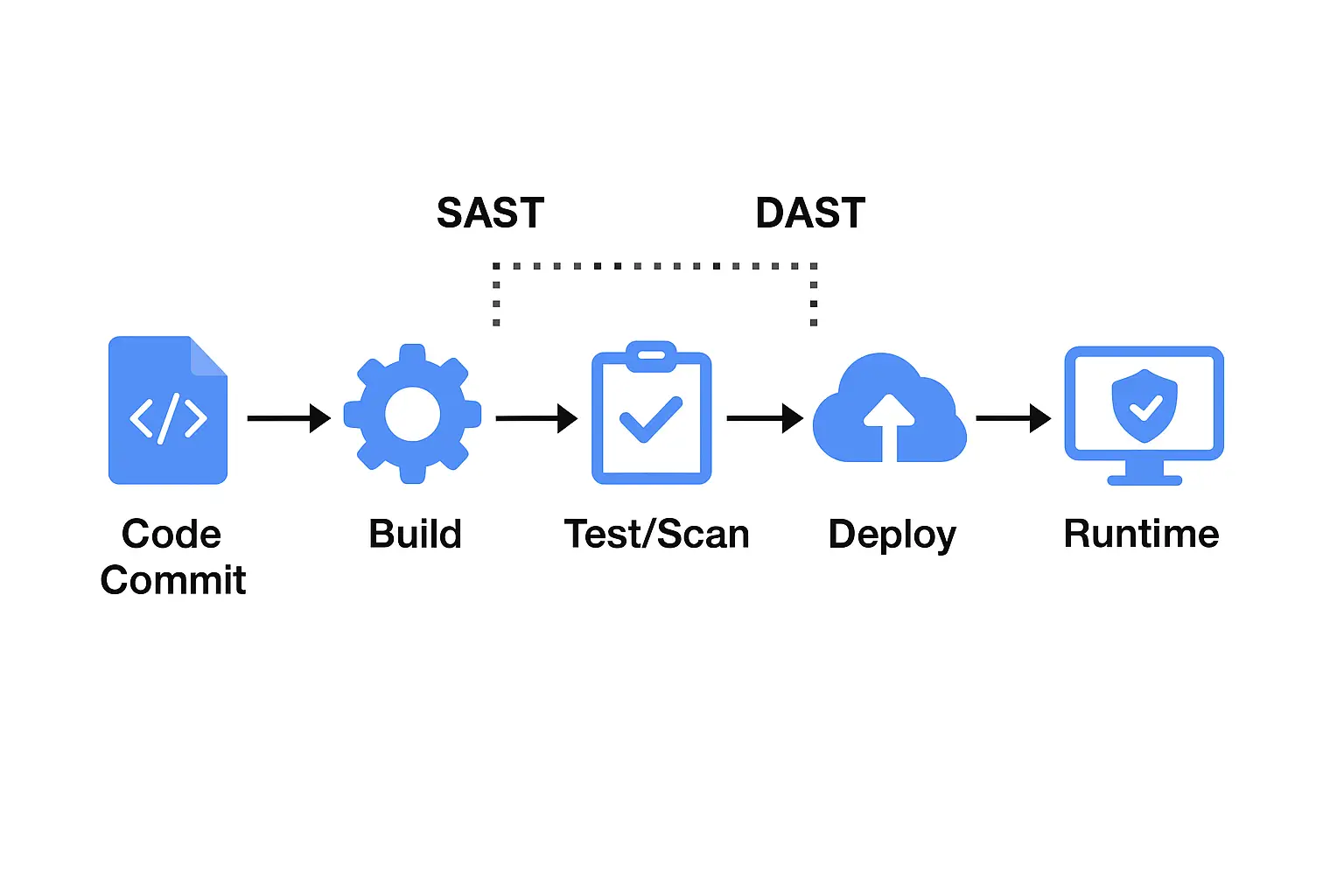
AI coding tools are making developers faster — but faster development also requires better visibility, stronger review workflows, and more reliable remediation. This is a practical governance guide for teams adopting Codex, Claude Code, Cursor, Windsurf, and other AI coding agents.