Stop vulnerabilities and secrets before they ship.
Scan Docker container images, detect CVEs, hardcoded secrets, and compliance risks across registries.
Plexicus container security scans images, enforces Kubernetes policies, and blocks runtime threats to keep workloads safe and compliant
Pioneering teams are already inside
















Protect containerized applications from build to runtime. Detect vulnerabilities, misconfigurations, and threats in real time to ensure resilient and compliant deployments.
Scan Docker container images, detect CVEs, hardcoded secrets, and compliance risks across registries.
Enforce RBAC, Pod Security Standards, and network policies automatically.
Detect cryptojacking, privilege escalation, and lateral movement with auto-response actions.
Generate SBOMs, validate licenses, and sign container images to secure your supply chain.
Plug Plexicus into GitLab, Jenkins, or GitHub Actions for container security monitoring during development.
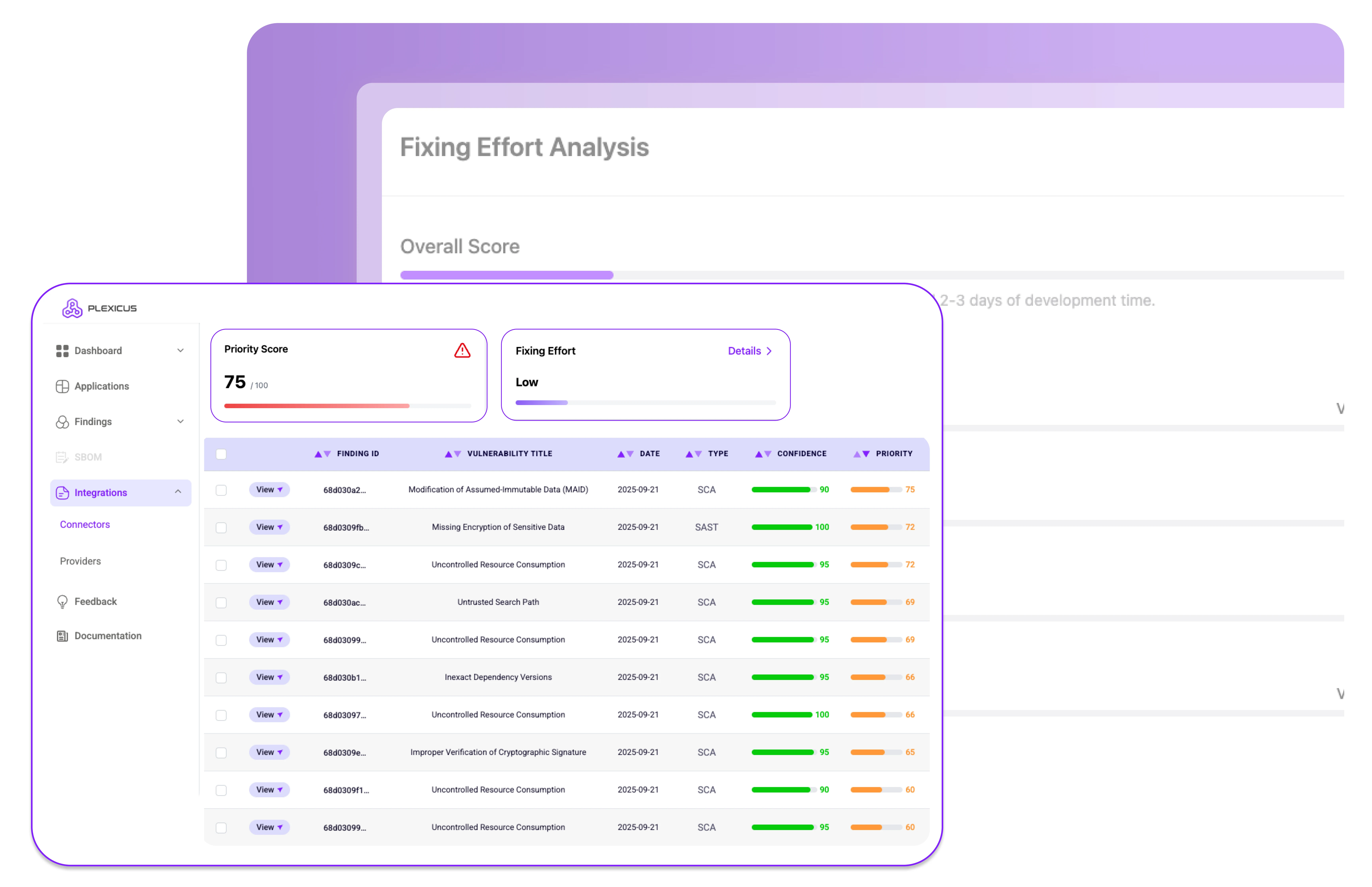
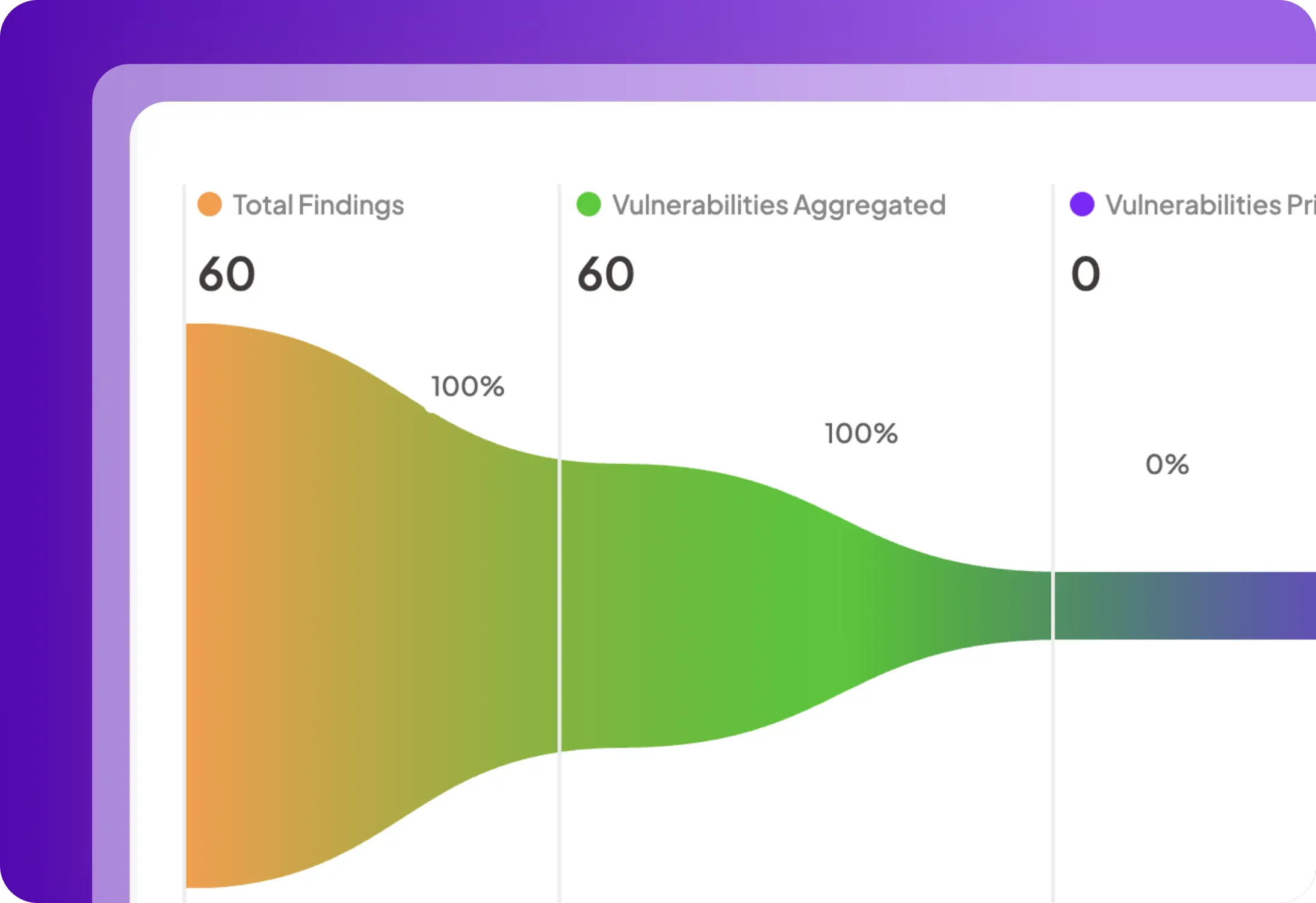
Comprehensive safeguards across build, deploy, and runtime with real-time visibility and defense.
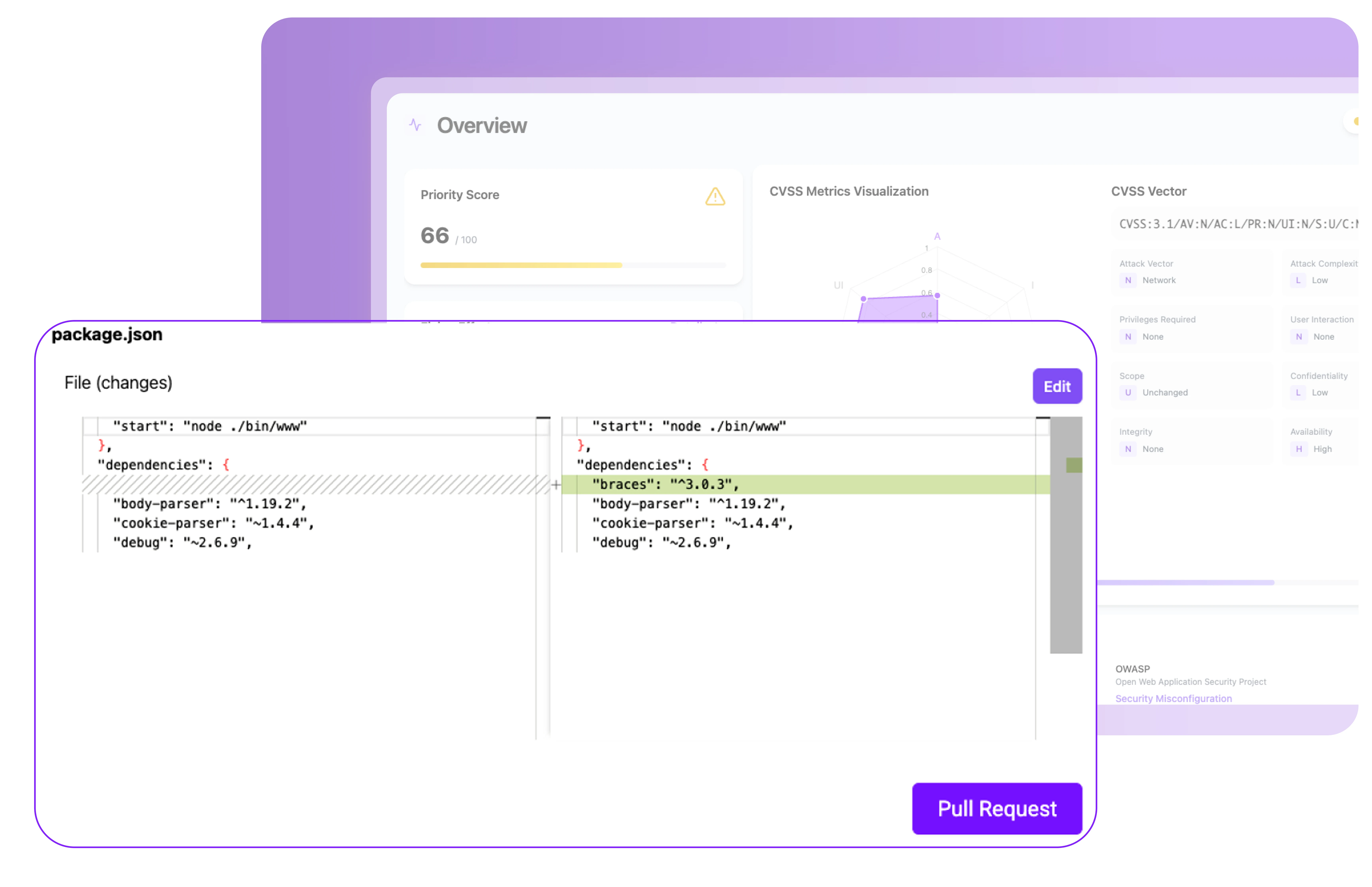
Scan container images during the build process to uncover vulnerabilities in base images, OS packages, and dependencies. Generate an SBOM for full visibility and ensure issues are caught before deployment.
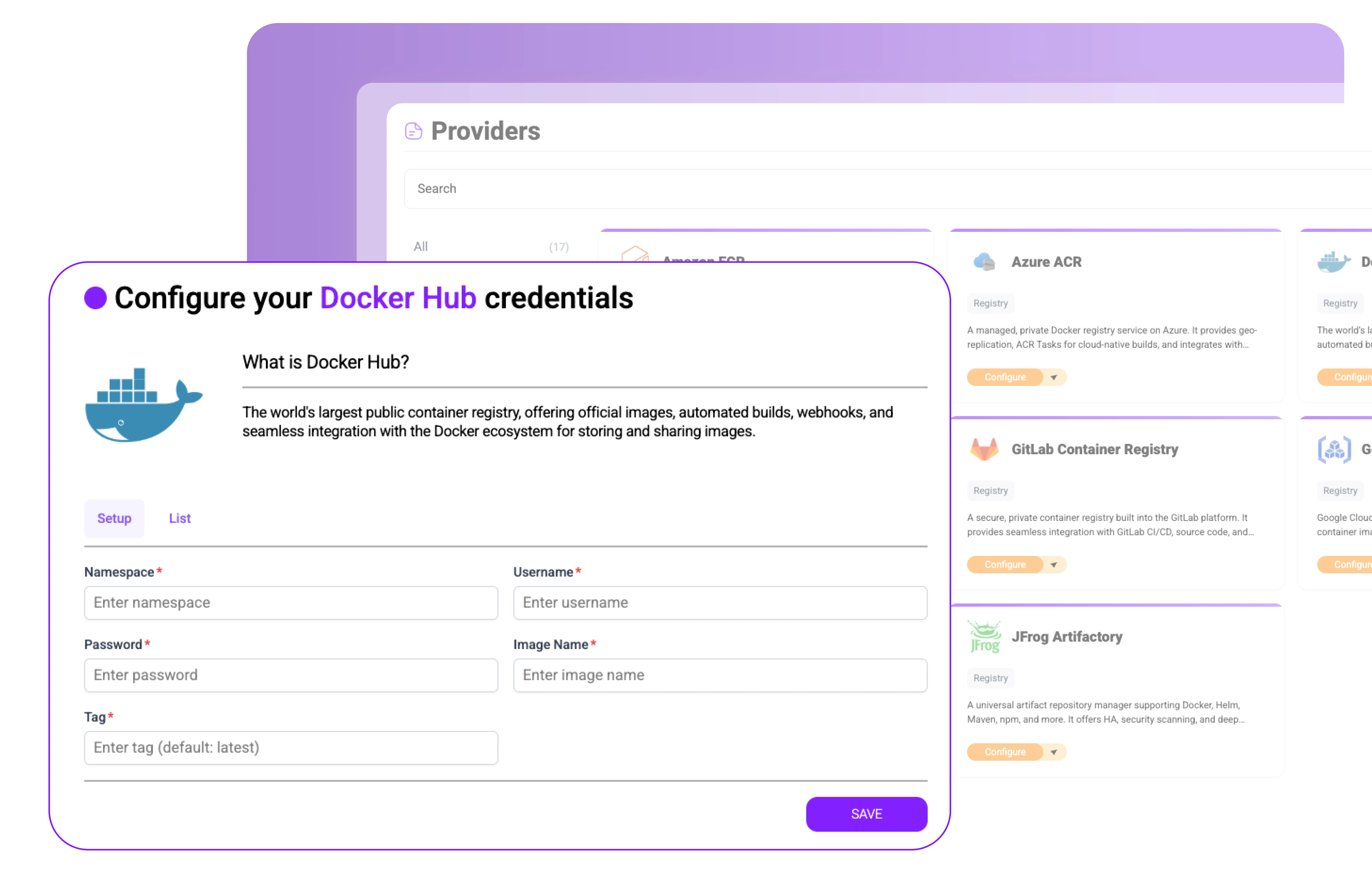
Integrate with registries like Docker Hub, AWS ECR, Azure ACR, and GCR. Automatically scan and sign images, detect secrets or malware, and enforce policies before containers are ever pulled into production.
Validate Kubernetes deployments with CIS Benchmarks, Pod Security Standards, and admission control policies.
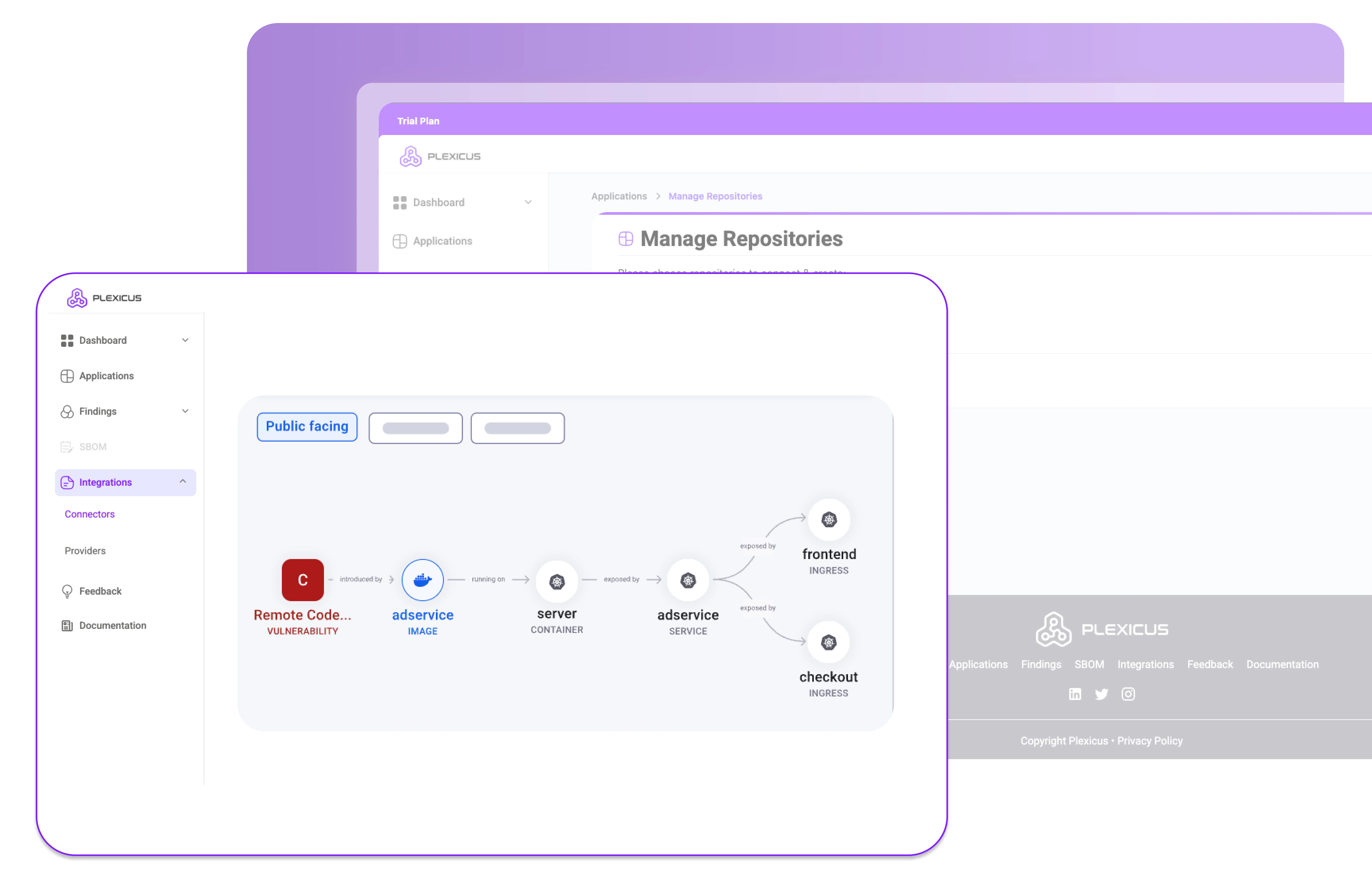
Monitor processes, network activity, and file integrity to detect and stop container threats in real time.
Connect Plexicus Container Security with your CI/CD pipelines, registries, and Kubernetes environments to secure containers without slowing development
Plexicus makes application container security easy, from build to runtime.
Install Plexicus Container Security in registries & clusters
Catch vulnerabilities and misconfigurations early.
Block runtime threats before damage is done
Join the teams who trust Plexicus to secure the code their AI writes — and the code they inherited.
As pioneers in cloud security, we've found Plexicus to be remarkably innovative in the vulnerability remediation space. The fact that they've integrated Prowler as one of their connectors demonstrates their commitment to leveraging the best open-source tools while adding significant value through their AI-powered remediation capabilities.

The AI agent's ability to automatically generate fixes for vulnerabilities has transformed our workflow.

As one of Plexicus's first customers, we've witnessed firsthand how their platform has evolved into an indispensable security solution. Their AI-powered remediation has dramatically reduced our vulnerability management overhead and allowed our security team to focus on strategic initiatives instead of repetitive fixes.

Plexicus's powerful vulnerability management allows us at Puffin Security to deliver more advanced cybersecurity services to our clients, creating a perfect security partnership.

Plexicus has revolutionized our remediation process - our team is saving hours every week!

The integration is seamless, and the AI-powered auto-remediation is a game-changer.

Plexicus has become an essential part of our security toolkit. It's like having an expert security engineer available 24/7.

Since implementing Plexicus, we've seen a dramatic improvement in our security posture with minimal effort from our team. The AI-driven approach to vulnerability remediation is truly revolutionary.

As pioneers in cloud security, we've found Plexicus to be remarkably innovative in the vulnerability remediation space. The fact that they've integrated Prowler as one of their connectors demonstrates their commitment to leveraging the best open-source tools while adding significant value through their AI-powered remediation capabilities.

The AI agent's ability to automatically generate fixes for vulnerabilities has transformed our workflow.

As one of Plexicus's first customers, we've witnessed firsthand how their platform has evolved into an indispensable security solution. Their AI-powered remediation has dramatically reduced our vulnerability management overhead and allowed our security team to focus on strategic initiatives instead of repetitive fixes.

Plexicus's powerful vulnerability management allows us at Puffin Security to deliver more advanced cybersecurity services to our clients, creating a perfect security partnership.

Plexicus has revolutionized our remediation process - our team is saving hours every week!

The integration is seamless, and the AI-powered auto-remediation is a game-changer.

Plexicus has become an essential part of our security toolkit. It's like having an expert security engineer available 24/7.

Since implementing Plexicus, we've seen a dramatic improvement in our security posture with minimal effort from our team. The AI-driven approach to vulnerability remediation is truly revolutionary.


Stop choosing between AI velocity and security debt. Plexicus is the only platform that runs Vibe Coding Security and ASPM in parallel — one workflow, every codebase.