Containers
Docker, Podman, Kubernetes pods
Cloud Workload Protection Platform
67% of breaches start in cloud workloads. Traditional antivirus doesn"t work in containers. Runtime threats bypass perimeter security. Plexicus CWPP detects and stops attacks inside your running workloads.
of breaches start in cloud workloads
average threat detection time
threat containment success rate
average CPU overhead
Unified Protection Across All Environments
Docker, Podman, Kubernetes pods
EC2, Azure VMs, GCE, on-prem
Lambda, Cloud Functions, Azure Functions
Comprehensive telemetry analysis across containers, virtual machines, and serverless functions
Deep Packet Inspection & Threat Intelligence
Inspect every packet leaving and entering your workloads in real time.
Match traffic against continuously updated threat signature databases.
Block IPs, domains and TTPs flagged by global intel feeds.
Detect deviations from baseline workload network behavior.
Packets Processed
per day, per cluster
Threats Blocked
last 30 days
Detection Rate
across CVE classes
Interactive Threat Triage Console - Unified analysis for ML anomalies and signature-based detection
Models learn each workload baseline and flag deviations within seconds.
Continuously updated indicators of compromise across known attack TTPs.
Causal process trees show every step from first touch to lateral movement.
Quarantine, kill, or restart compromised workloads with policy-driven actions.
Watch how Plexicus seamlessly integrates across your entire development workflow, from IDE to production, providing intelligent security without disrupting your flow.
Following a threat through the daily workflow
Adding a malicious dependency
Threat enters the repository
Public confrontation begins
Plexicus detects the threat
Complete threat analysis
Interactive dashboard for real-time threat analysis and response
Live CPU, memory, disk and network telemetry per workload.
Active inbound and outbound flows with origin reputation scoring.
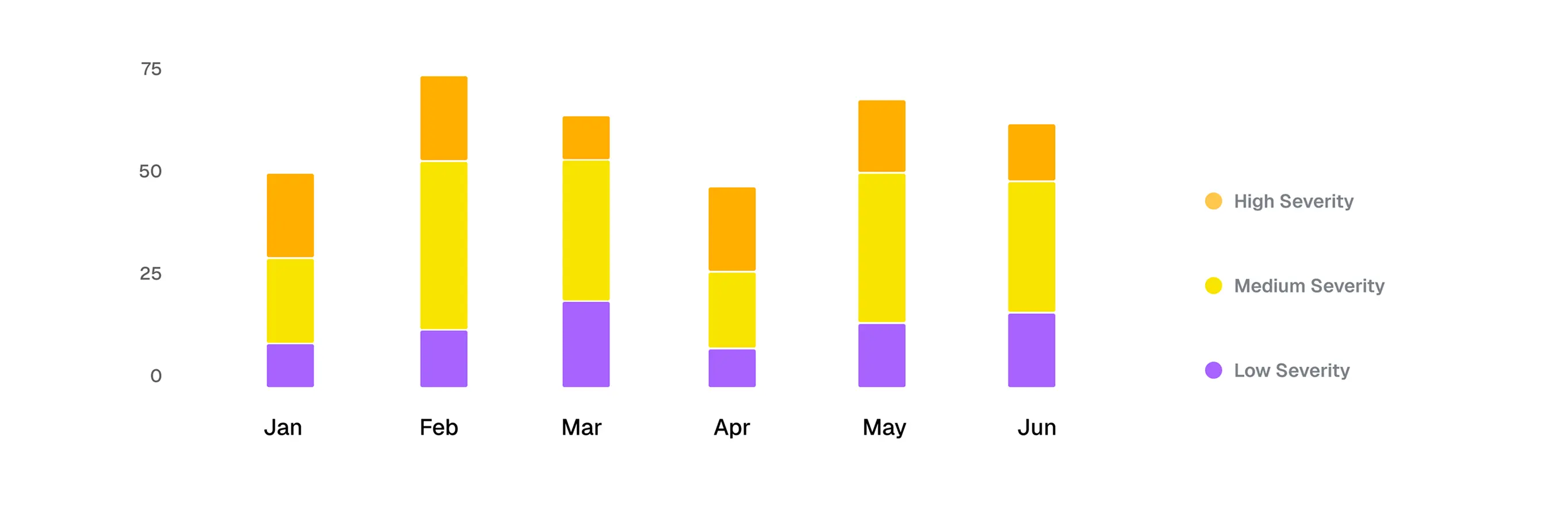
Severity-ranked stream of detections from every cluster.
One click reveals process tree, network graph and policy match.
Integration, Governance & Onboarding Console

Plexicus is the AI-native ASPM that scans, filters, fixes, pentests, and explains — autonomously. Unlimited developers, unlimited repos, fair-use AI actions. Real free tier, €269/mo annual when you're ready.