Stop sårbarheder og hemmeligheder før de sendes.
Scan Docker container billeder, detekter CVE'er, hardkodede hemmeligheder, og overholdelsesrisici på tværs af registreringer.
Plexicus container sikkerhed scanner billeder, håndhæver Kubernetes politikker, og blokerer runtime trusler for at holde arbejdsbelastninger sikre og i overensstemmelse
Førende teams er allerede med
















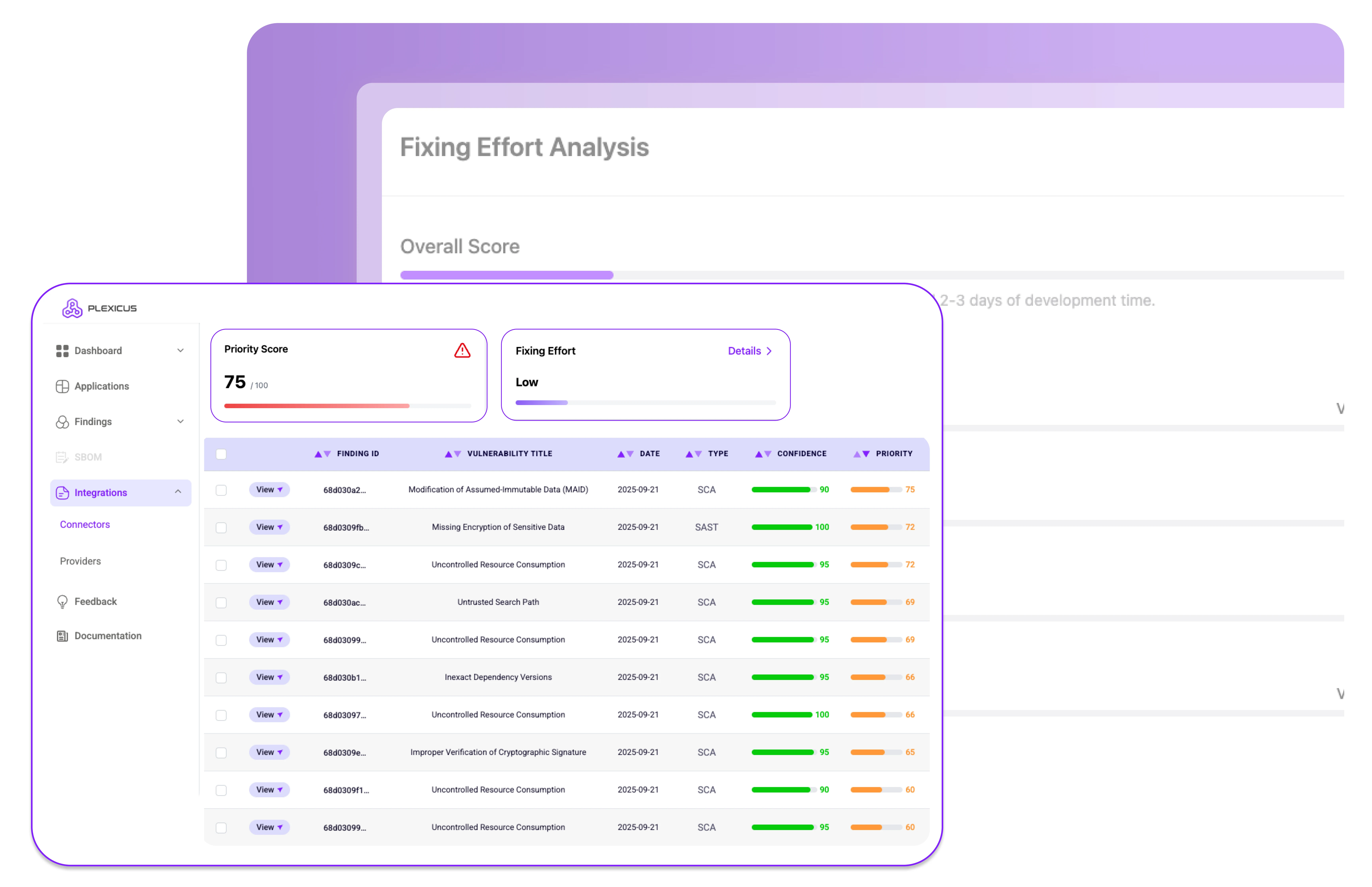
Beskyt containeriserede applikationer fra opbygning til kørsel. Opdag sårbarheder, fejlkonfigurationer og trusler i realtid for at sikre robuste og overholdelsesvenlige implementeringer.
Scan Docker container billeder, detekter CVE'er, hardkodede hemmeligheder, og overholdelsesrisici på tværs af registreringer.
Håndhæv RBAC, Pod Security Standards, og netværkspolitikker automatisk.
Detekter kryptojacking, privilegieeskalering, og lateral bevægelse med auto-respons handlinger.
Generer SBOM'er, valider licenser, og signer container billeder for at sikre din forsyningskæde.
Tilslut Plexicus til GitLab, Jenkins, eller GitHub Actions for container sikkerhedsovervågning under udvikling.
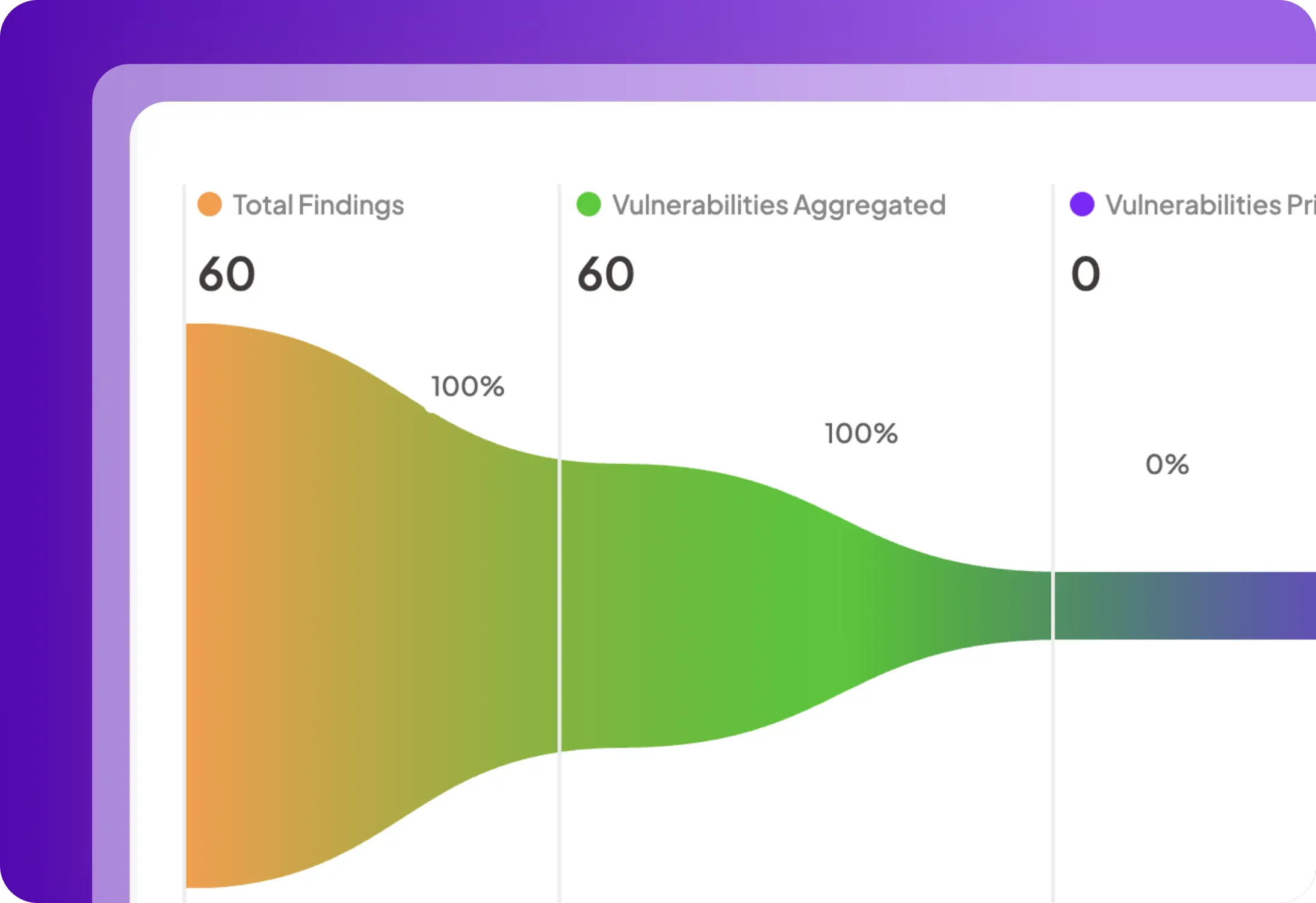
Omfattende beskyttelse på tværs af opbygning, implementering og kørsel med realtids synlighed og forsvar.
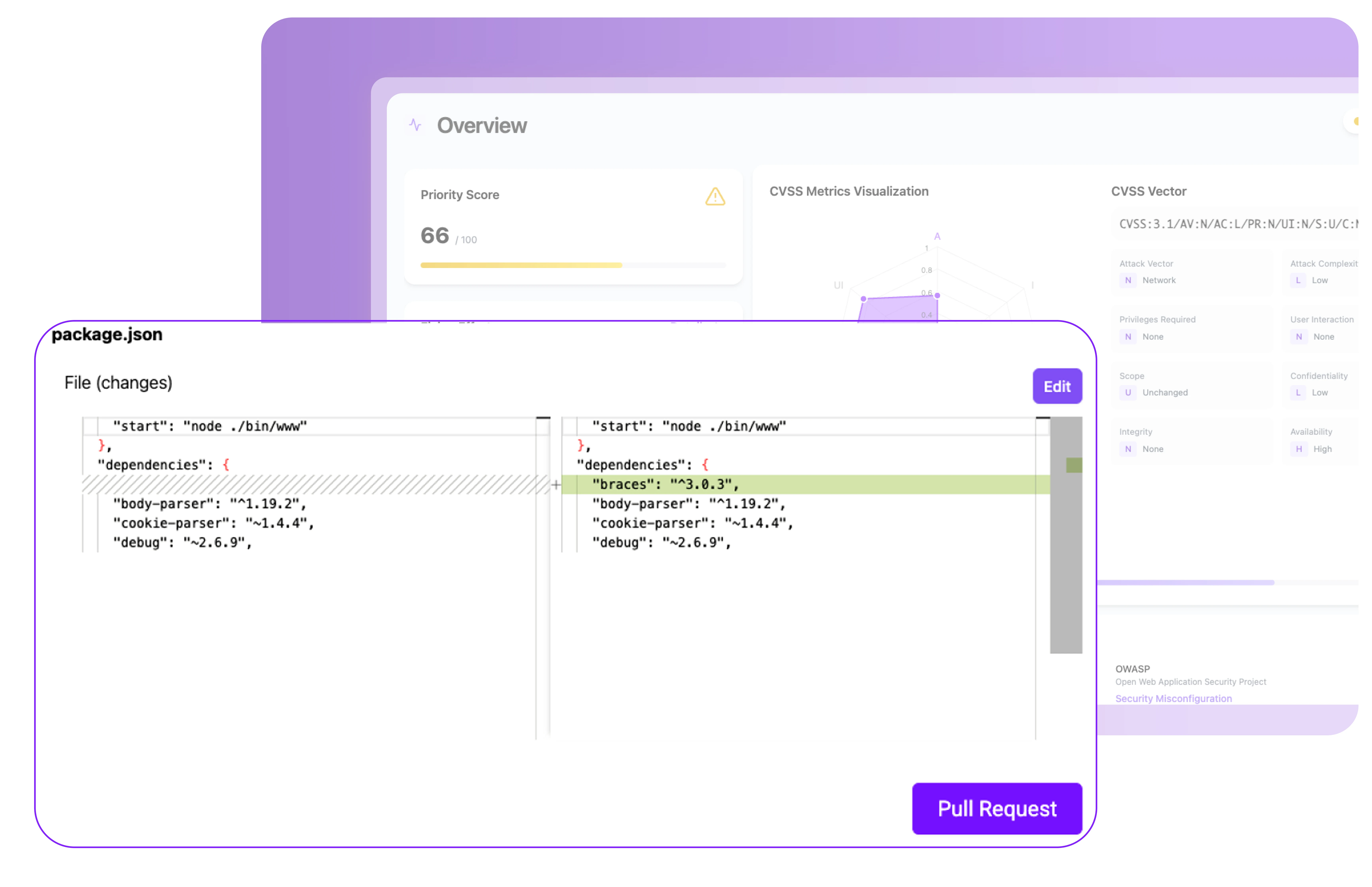
Scan containerbilleder under opbygningsprocessen for at afsløre sårbarheder i basebilleder, OS-pakker og afhængigheder. Generer en SBOM for fuld synlighed og sørg for, at problemer opdages før implementering.
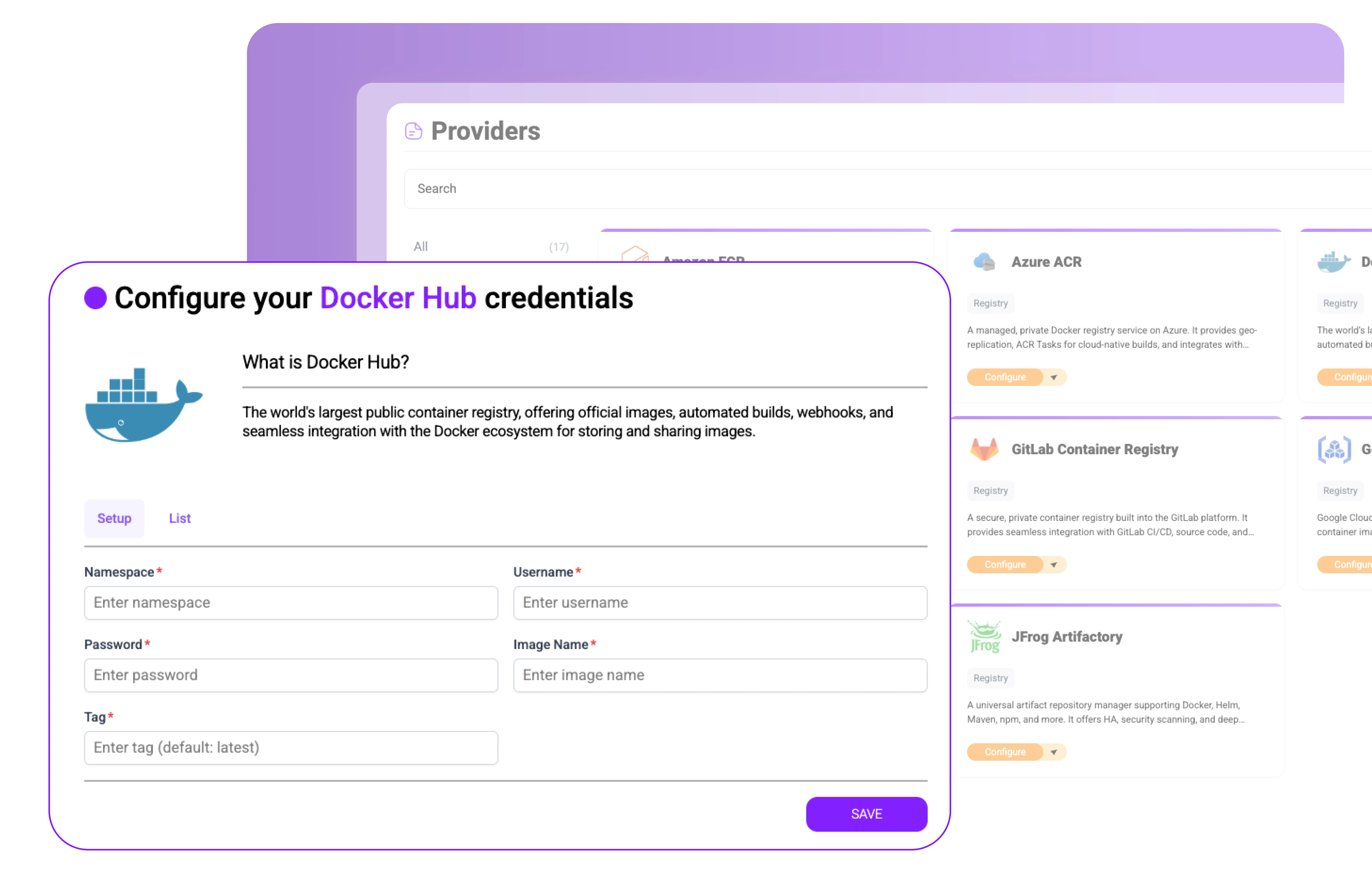
Integrer med registries som Docker Hub, AWS ECR, Azure ACR og GCR. Scan og signér automatisk billeder, opdag hemmeligheder eller malware, og håndhæv politikker, før containere nogensinde trækkes ind i produktion.
Valider Kubernetes-implementeringer med CIS Benchmarks, Pod Security Standards og adgangskontrolpolitikker.
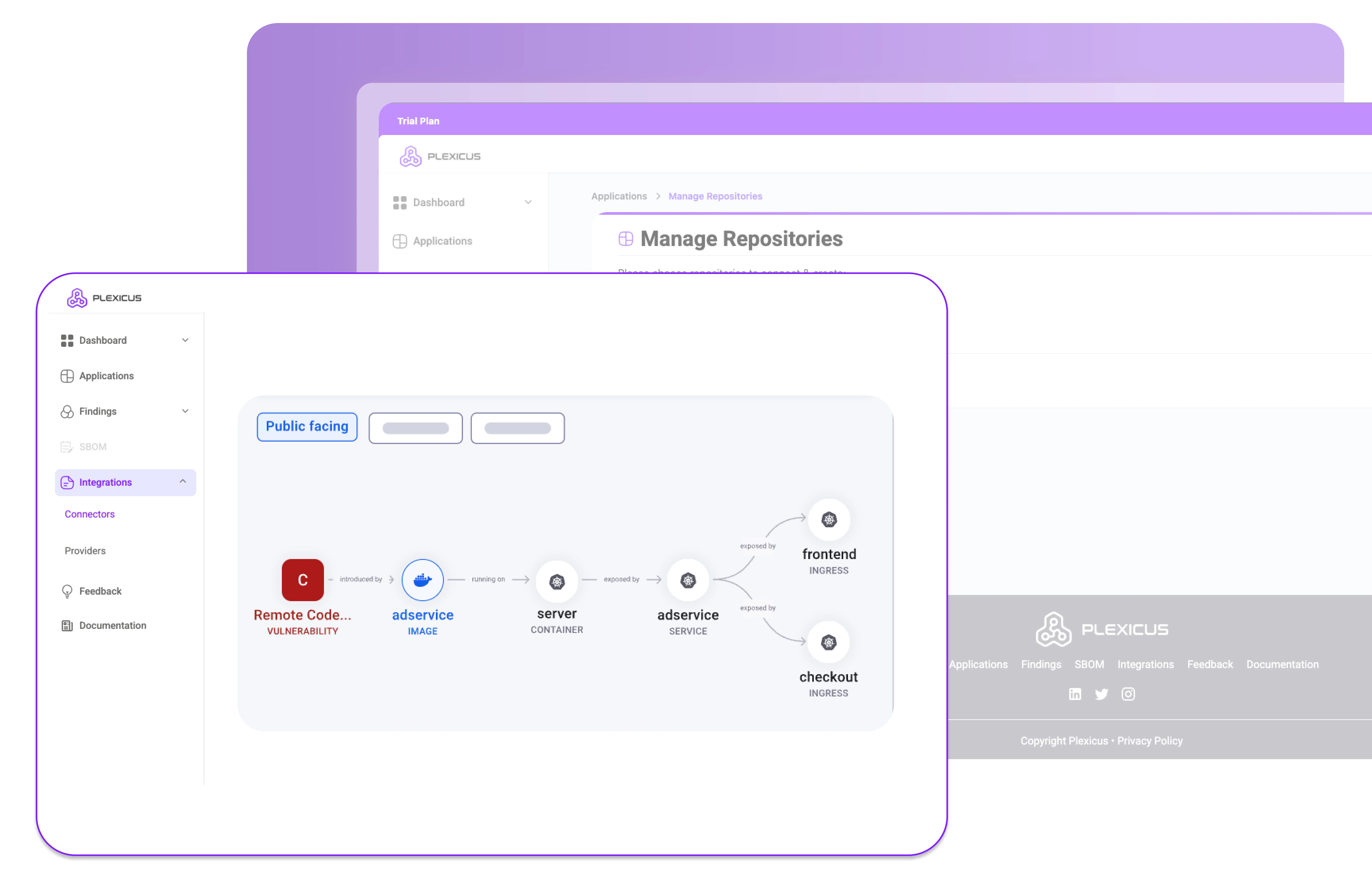
Overvåg processer, netværksaktivitet og filintegritet for at opdage og stoppe containertrusler i realtid.
Forbind Plexicus Container Security med dine CI/CD-pipelines, registries og Kubernetes-miljøer for at sikre containere uden at bremse udviklingen
Plexicus gør applikationsbeholdersikkerhed nem, fra bygning til kørsel.
Installer Plexicus Container Security i registre & klynger
Fang sårbarheder og fejlkonfigurationer tidligt.
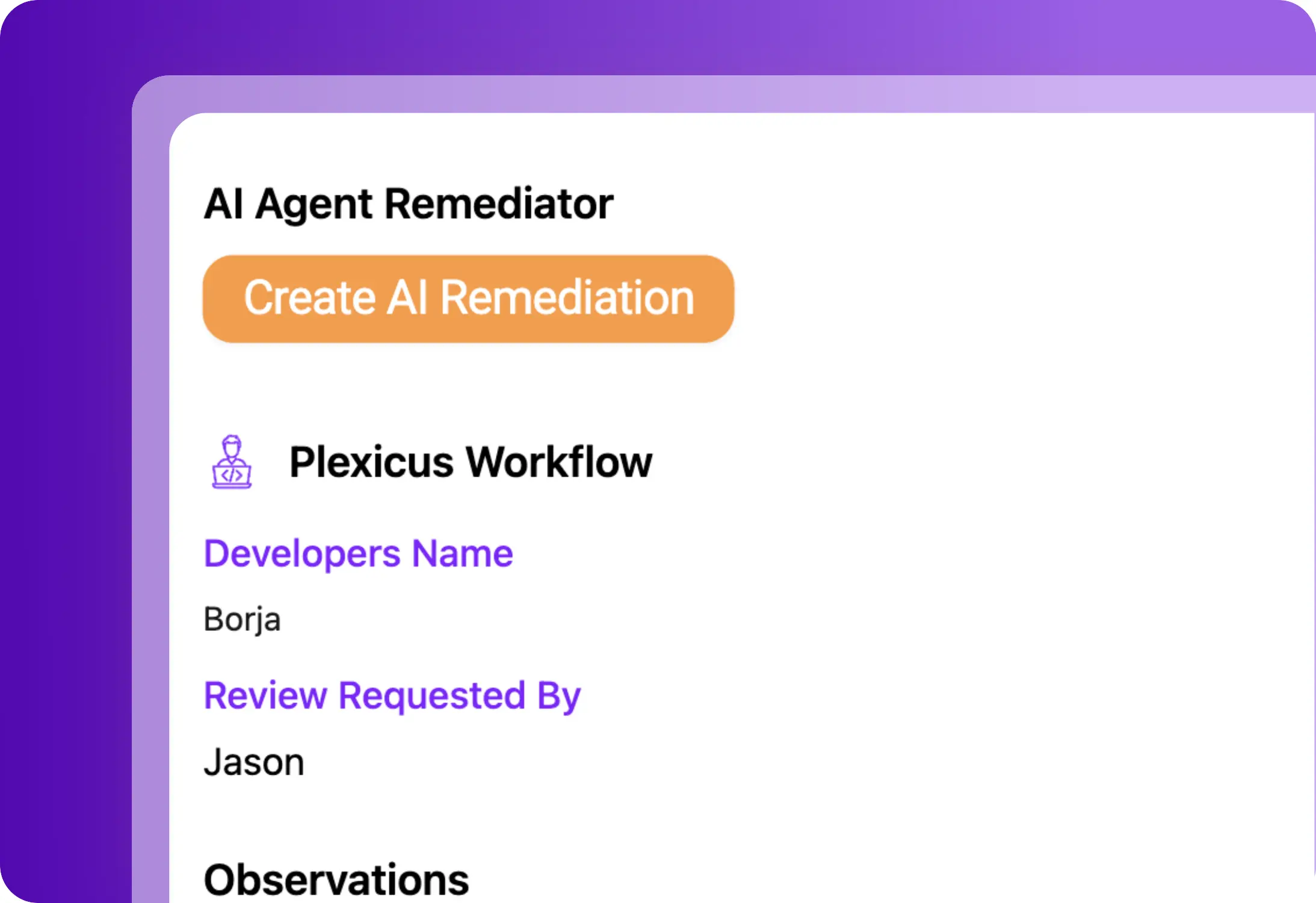
Bloker trusler i kørsel før skaden er sket
Slut dig til de teams, der betror Plexicus med at sikre den kode, deres AI skriver — og den kode, de har arvet.
As pioneers in cloud security, we've found Plexicus to be remarkably innovative in the vulnerability remediation space. The fact that they've integrated Prowler as one of their connectors demonstrates their commitment to leveraging the best open-source tools while adding significant value through their AI-powered remediation capabilities.

The AI agent's ability to automatically generate fixes for vulnerabilities has transformed our workflow.

As one of Plexicus's first customers, we've witnessed firsthand how their platform has evolved into an indispensable security solution. Their AI-powered remediation has dramatically reduced our vulnerability management overhead and allowed our security team to focus on strategic initiatives instead of repetitive fixes.

Plexicus's powerful vulnerability management allows us at Puffin Security to deliver more advanced cybersecurity services to our clients, creating a perfect security partnership.

Plexicus has revolutionized our remediation process - our team is saving hours every week!

The integration is seamless, and the AI-powered auto-remediation is a game-changer.

Plexicus has become an essential part of our security toolkit. It's like having an expert security engineer available 24/7.

Since implementing Plexicus, we've seen a dramatic improvement in our security posture with minimal effort from our team. The AI-driven approach to vulnerability remediation is truly revolutionary.

As pioneers in cloud security, we've found Plexicus to be remarkably innovative in the vulnerability remediation space. The fact that they've integrated Prowler as one of their connectors demonstrates their commitment to leveraging the best open-source tools while adding significant value through their AI-powered remediation capabilities.

The AI agent's ability to automatically generate fixes for vulnerabilities has transformed our workflow.

As one of Plexicus's first customers, we've witnessed firsthand how their platform has evolved into an indispensable security solution. Their AI-powered remediation has dramatically reduced our vulnerability management overhead and allowed our security team to focus on strategic initiatives instead of repetitive fixes.

Plexicus's powerful vulnerability management allows us at Puffin Security to deliver more advanced cybersecurity services to our clients, creating a perfect security partnership.

Plexicus has revolutionized our remediation process - our team is saving hours every week!

The integration is seamless, and the AI-powered auto-remediation is a game-changer.

Plexicus has become an essential part of our security toolkit. It's like having an expert security engineer available 24/7.

Since implementing Plexicus, we've seen a dramatic improvement in our security posture with minimal effort from our team. The AI-driven approach to vulnerability remediation is truly revolutionary.


Hold op med at vælge mellem AI-tempo og sikkerhedsgæld. Plexicus er den eneste platform, der kører Vibe Coding Security og ASPM parallelt — ét workflow, hver eneste codebase.