Hentikan kerentanan dan rahasia sebelum dikirim.
Pindai gambar kontainer Docker, deteksi CVE, rahasia yang dikodekan keras, dan risiko kepatuhan di seluruh registri.
Keamanan kontainer Plexicus memindai gambar, menegakkan kebijakan Kubernetes, dan memblokir ancaman waktu aktif untuk menjaga beban kerja tetap aman dan sesuai.
Tim-tim pelopor sudah bergabung
















Lindungi aplikasi terkontainerisasi dari build hingga runtime. Deteksi kerentanan, salah konfigurasi, dan ancaman secara real-time untuk memastikan penerapan yang tangguh dan sesuai.
Pindai gambar kontainer Docker, deteksi CVE, rahasia yang dikodekan keras, dan risiko kepatuhan di seluruh registri.
Terapkan RBAC, Standar Keamanan Pod, dan kebijakan jaringan secara otomatis.
Deteksi cryptojacking, eskalasi hak istimewa, dan pergerakan lateral dengan tindakan respons otomatis.
Hasilkan SBOM, validasi lisensi, dan tandatangani gambar kontainer untuk mengamankan rantai pasokan Anda.
Hubungkan Plexicus ke GitLab, Jenkins, atau GitHub Actions untuk pemantauan keamanan kontainer selama pengembangan.
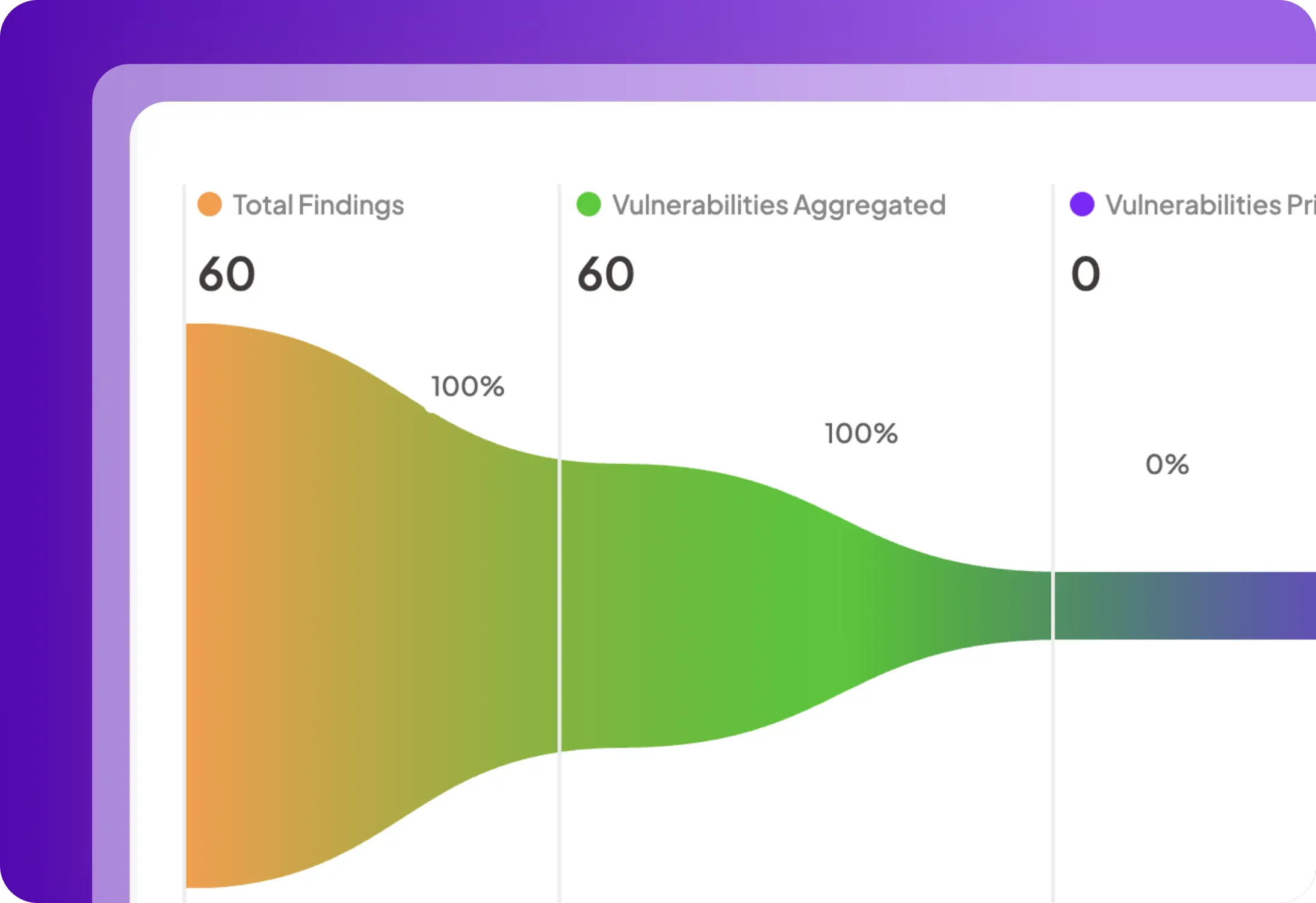
Perlindungan komprehensif di seluruh build, deploy, dan runtime dengan visibilitas dan pertahanan real-time.
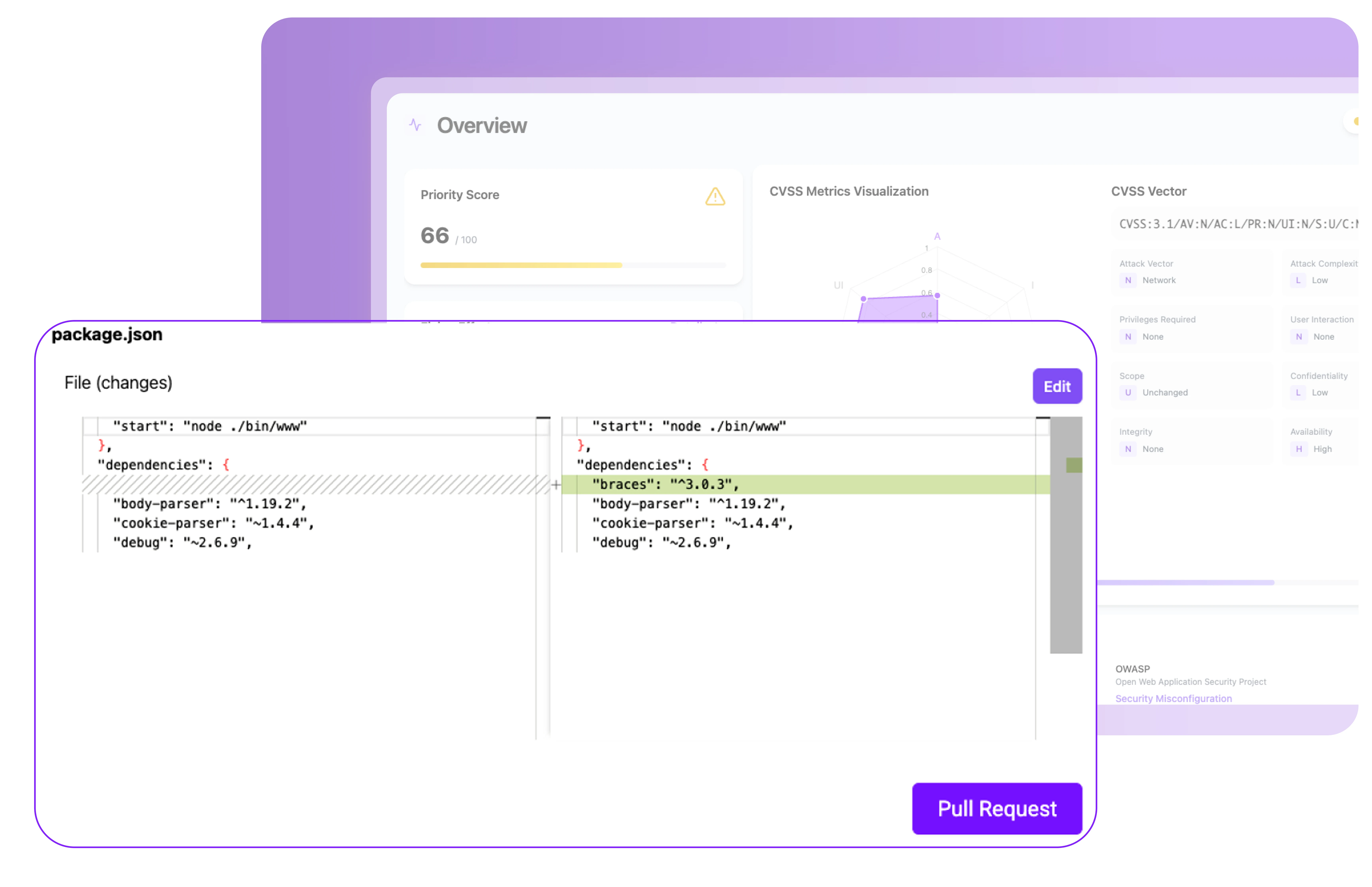
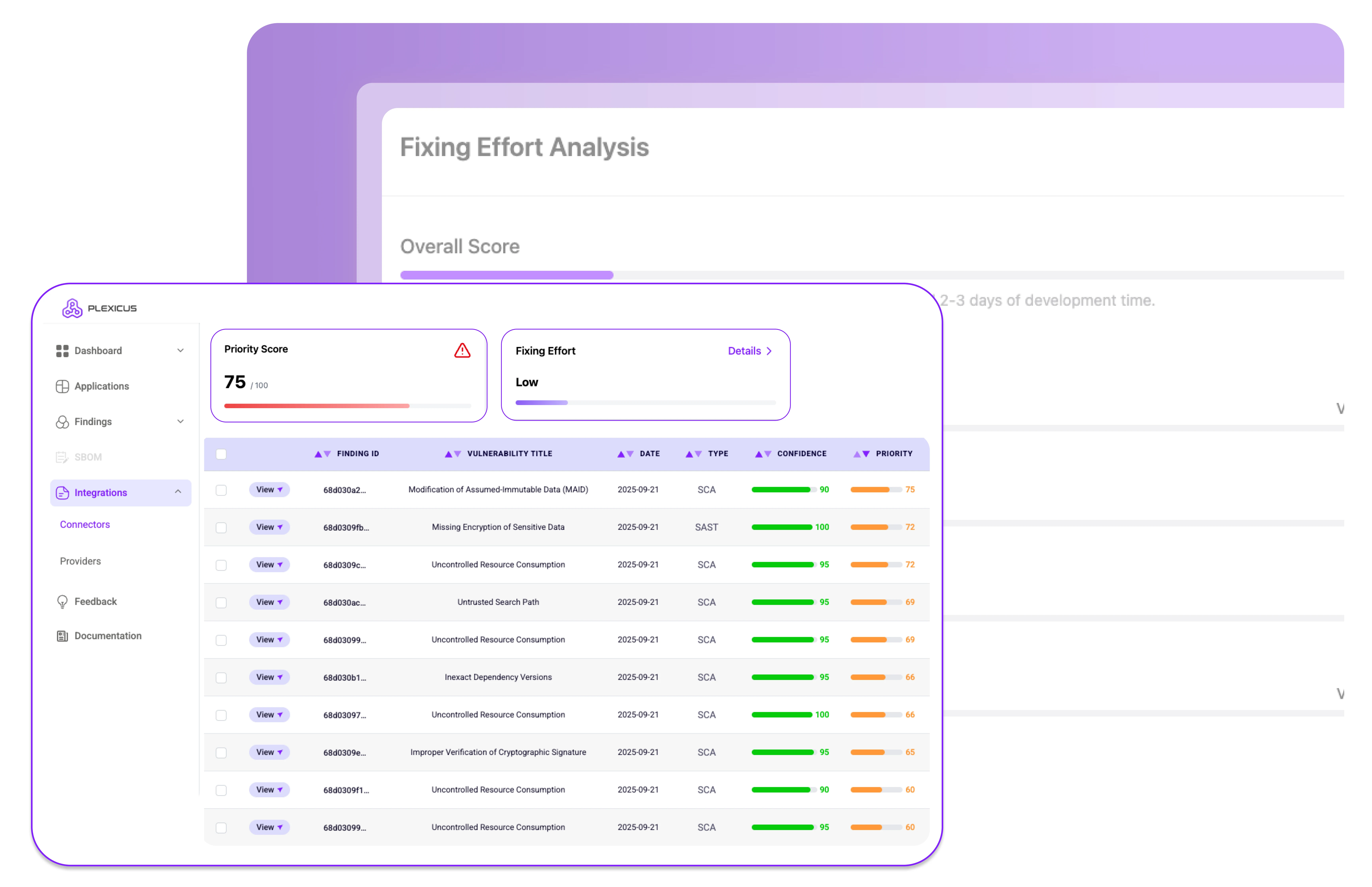
Pindai gambar kontainer selama proses build untuk mengungkap kerentanan dalam gambar dasar, paket OS, dan dependensi. Hasilkan SBOM untuk visibilitas penuh dan pastikan masalah terdeteksi sebelum penerapan.
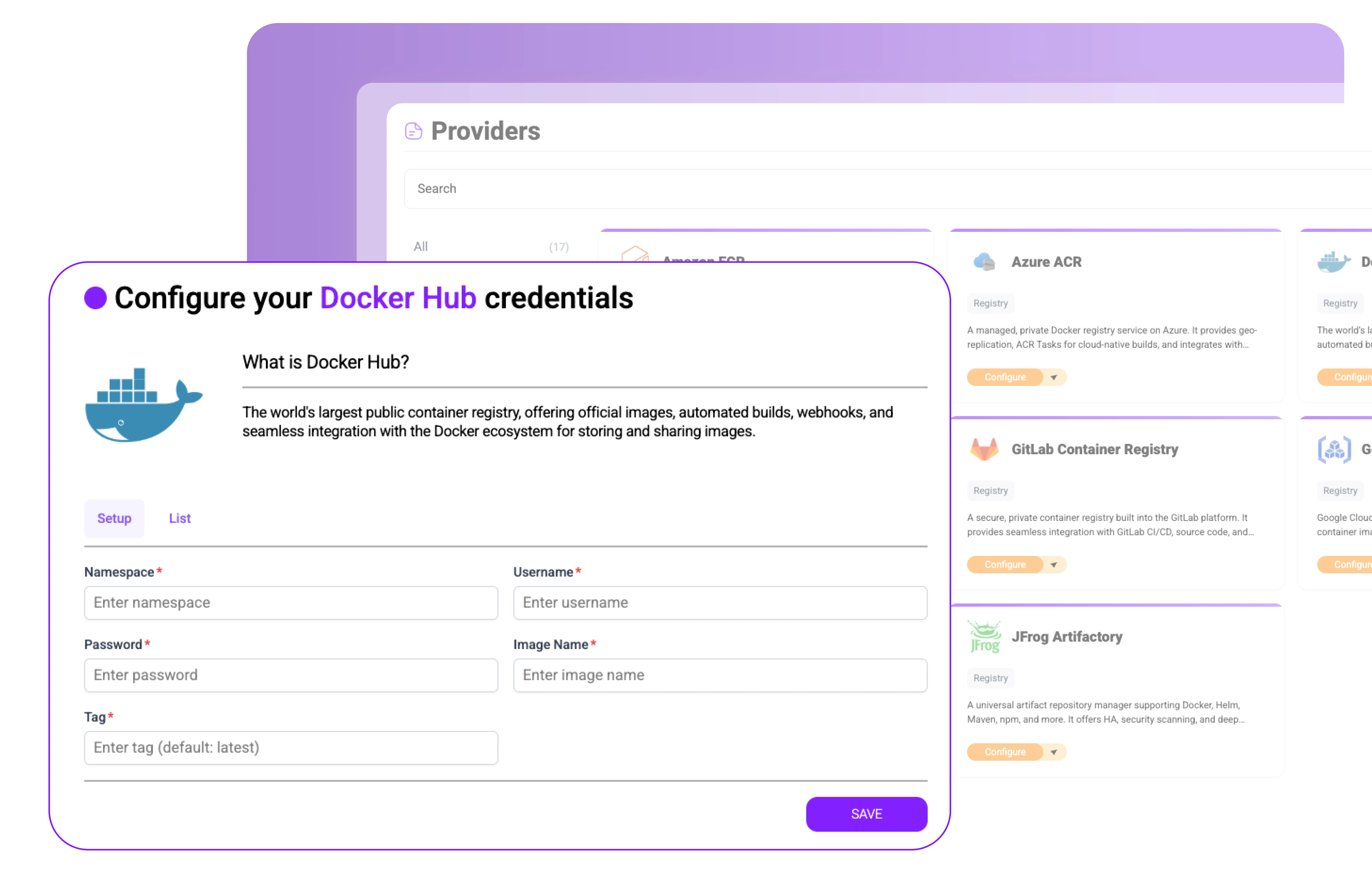
Integrasikan dengan registri seperti Docker Hub, AWS ECR, Azure ACR, dan GCR. Pindai dan tandatangani gambar secara otomatis, deteksi rahasia atau malware, dan terapkan kebijakan sebelum kontainer ditarik ke produksi.
Validasi penerapan Kubernetes dengan CIS Benchmarks, Standar Keamanan Pod, dan kebijakan kontrol penerimaan.
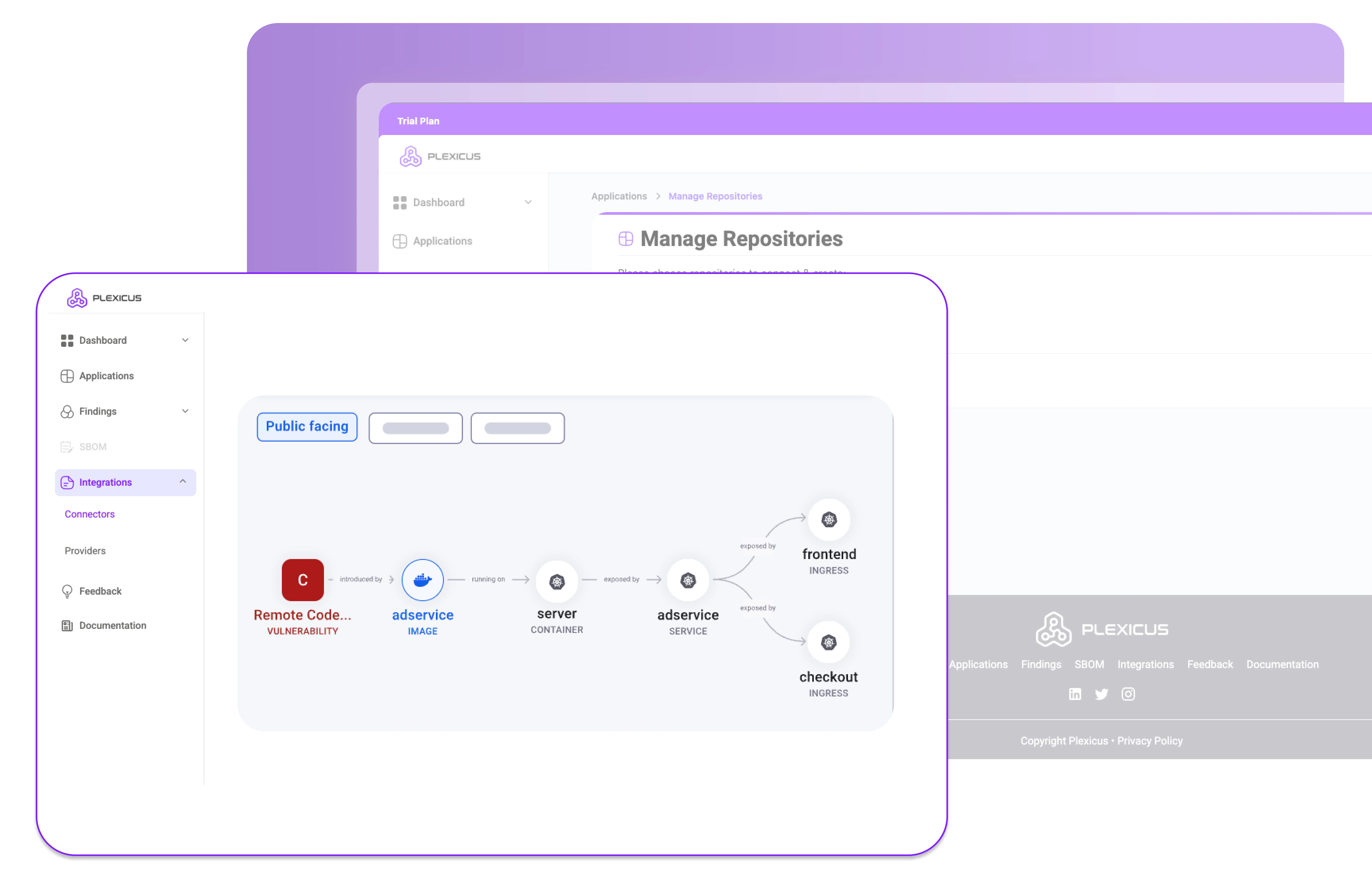
Pantau proses, aktivitas jaringan, dan integritas file untuk mendeteksi dan menghentikan ancaman kontainer secara real-time.
Hubungkan Plexicus Container Security dengan pipeline CI/CD, registri, dan lingkungan Kubernetes Anda untuk mengamankan kontainer tanpa memperlambat pengembangan
Plexicus membuat keamanan kontainer aplikasi mudah, dari pembangunan hingga runtime.
Pasang Keamanan Kontainer Plexicus di registri & kluster
Tangkap kerentanan dan salah konfigurasi lebih awal.
Blokir ancaman runtime sebelum kerusakan terjadi
Bergabunglah dengan tim yang mempercayakan Plexicus untuk mengamankan kode yang ditulis AI mereka — dan kode yang mereka warisi.
As pioneers in cloud security, we've found Plexicus to be remarkably innovative in the vulnerability remediation space. The fact that they've integrated Prowler as one of their connectors demonstrates their commitment to leveraging the best open-source tools while adding significant value through their AI-powered remediation capabilities.

The AI agent's ability to automatically generate fixes for vulnerabilities has transformed our workflow.

As one of Plexicus's first customers, we've witnessed firsthand how their platform has evolved into an indispensable security solution. Their AI-powered remediation has dramatically reduced our vulnerability management overhead and allowed our security team to focus on strategic initiatives instead of repetitive fixes.

Plexicus's powerful vulnerability management allows us at Puffin Security to deliver more advanced cybersecurity services to our clients, creating a perfect security partnership.

Plexicus has revolutionized our remediation process - our team is saving hours every week!

The integration is seamless, and the AI-powered auto-remediation is a game-changer.

Plexicus has become an essential part of our security toolkit. It's like having an expert security engineer available 24/7.

Since implementing Plexicus, we've seen a dramatic improvement in our security posture with minimal effort from our team. The AI-driven approach to vulnerability remediation is truly revolutionary.

As pioneers in cloud security, we've found Plexicus to be remarkably innovative in the vulnerability remediation space. The fact that they've integrated Prowler as one of their connectors demonstrates their commitment to leveraging the best open-source tools while adding significant value through their AI-powered remediation capabilities.

The AI agent's ability to automatically generate fixes for vulnerabilities has transformed our workflow.

As one of Plexicus's first customers, we've witnessed firsthand how their platform has evolved into an indispensable security solution. Their AI-powered remediation has dramatically reduced our vulnerability management overhead and allowed our security team to focus on strategic initiatives instead of repetitive fixes.

Plexicus's powerful vulnerability management allows us at Puffin Security to deliver more advanced cybersecurity services to our clients, creating a perfect security partnership.

Plexicus has revolutionized our remediation process - our team is saving hours every week!

The integration is seamless, and the AI-powered auto-remediation is a game-changer.

Plexicus has become an essential part of our security toolkit. It's like having an expert security engineer available 24/7.

Since implementing Plexicus, we've seen a dramatic improvement in our security posture with minimal effort from our team. The AI-driven approach to vulnerability remediation is truly revolutionary.


Berhenti memilih antara kecepatan AI dan utang keamanan. Plexicus adalah satu-satunya platform yang menjalankan Vibe Coding Security dan ASPM secara paralel — satu workflow, semua codebase.