Kontainer
Docker, Podman, Kubernetes pods
Platform Perlindungan Beban Kerja Cloud
67% pelanggaran dimulai dalam beban kerja cloud. Antivirus tradisional tidak berfungsi dalam kontainer. Ancaman runtime melewati keamanan perimeter. Plexicus CWPP mendeteksi dan menghentikan serangan di dalam beban kerja Anda yang sedang berjalan.
pelanggaran dimulai dalam beban kerja cloud
waktu deteksi ancaman rata-rata
tingkat keberhasilan penahanan ancaman
overhead CPU rata-rata
Perlindungan Terpadu di Semua Lingkungan
Docker, Podman, Kubernetes pods
EC2, Azure VMs, GCE, on-prem
Lambda, Cloud Functions, Azure Functions
Analisis telemetri komprehensif di seluruh kontainer, mesin virtual, dan fungsi tanpa server
Inspeksi Paket Mendalam & Intelijen Ancaman
Inspect every packet leaving and entering your workloads in real time.
Match traffic against continuously updated threat signature databases.
Block IPs, domains and TTPs flagged by global intel feeds.
Detect deviations from baseline workload network behavior.
Paket Diproses
per day, per cluster
Ancaman Diblokir
last 30 days
Tingkat Deteksi
across CVE classes
Konsol Triage Ancaman Interaktif - Analisis terpadu untuk anomali ML dan deteksi berbasis tanda tangan
Models learn each workload baseline and flag deviations within seconds.
Continuously updated indicators of compromise across known attack TTPs.
Causal process trees show every step from first touch to lateral movement.
Quarantine, kill, or restart compromised workloads with policy-driven actions.
Saksikan bagaimana Plexicus terintegrasi dengan mulus di seluruh alur kerja pengembangan Anda, dari IDE hingga produksi, memberikan keamanan cerdas tanpa mengganggu alur Anda.
Mengikuti ancaman melalui alur kerja harian
Menambahkan ketergantungan berbahaya
Ancaman memasuki repositori
Konfrontasi publik dimulai
Plexicus mendeteksi ancaman
Analisis ancaman lengkap
Dasbor interaktif untuk analisis dan tanggapan ancaman waktu nyata
Live CPU, memory, disk and network telemetry per workload.
Active inbound and outbound flows with origin reputation scoring.
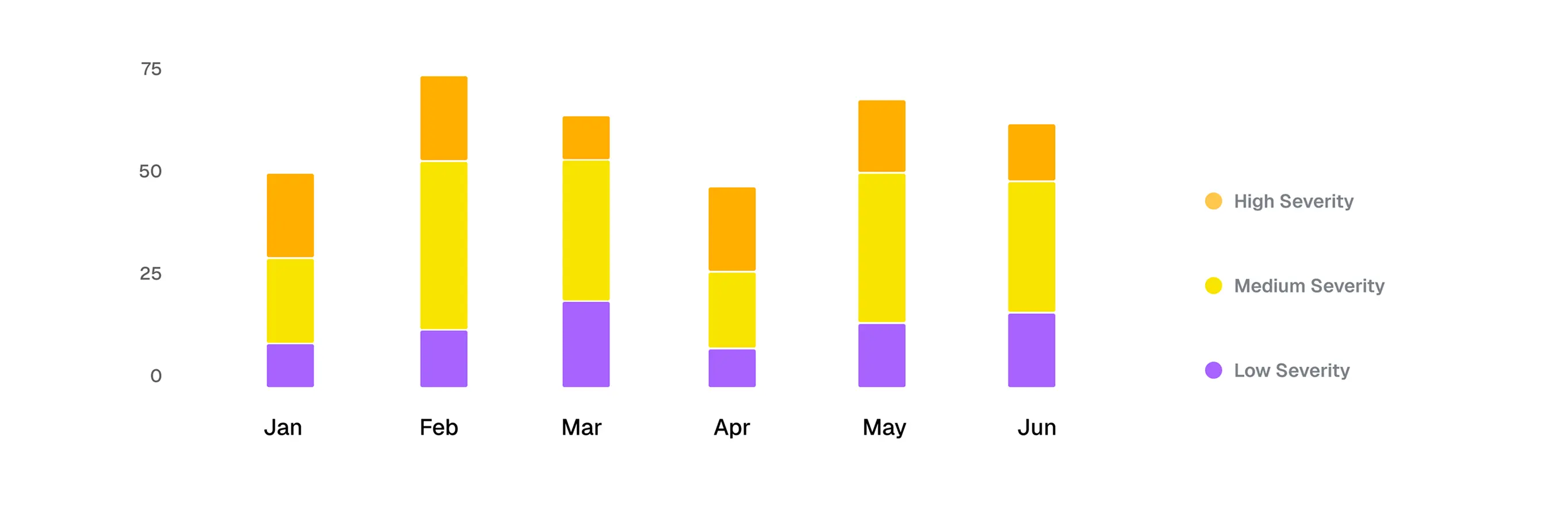
Severity-ranked stream of detections from every cluster.
One click reveals process tree, network graph and policy match.
Konsol Integrasi, Tata Kelola & Onboarding

Plexicus is the AI-native ASPM that scans, filters, fixes, pentests, and explains — autonomously. Unlimited developers, unlimited repos, fair-use AI actions. Real free tier, €269/mo annual when you're ready.