Stop kwetsbaarheden en geheimen voordat ze worden verzonden.
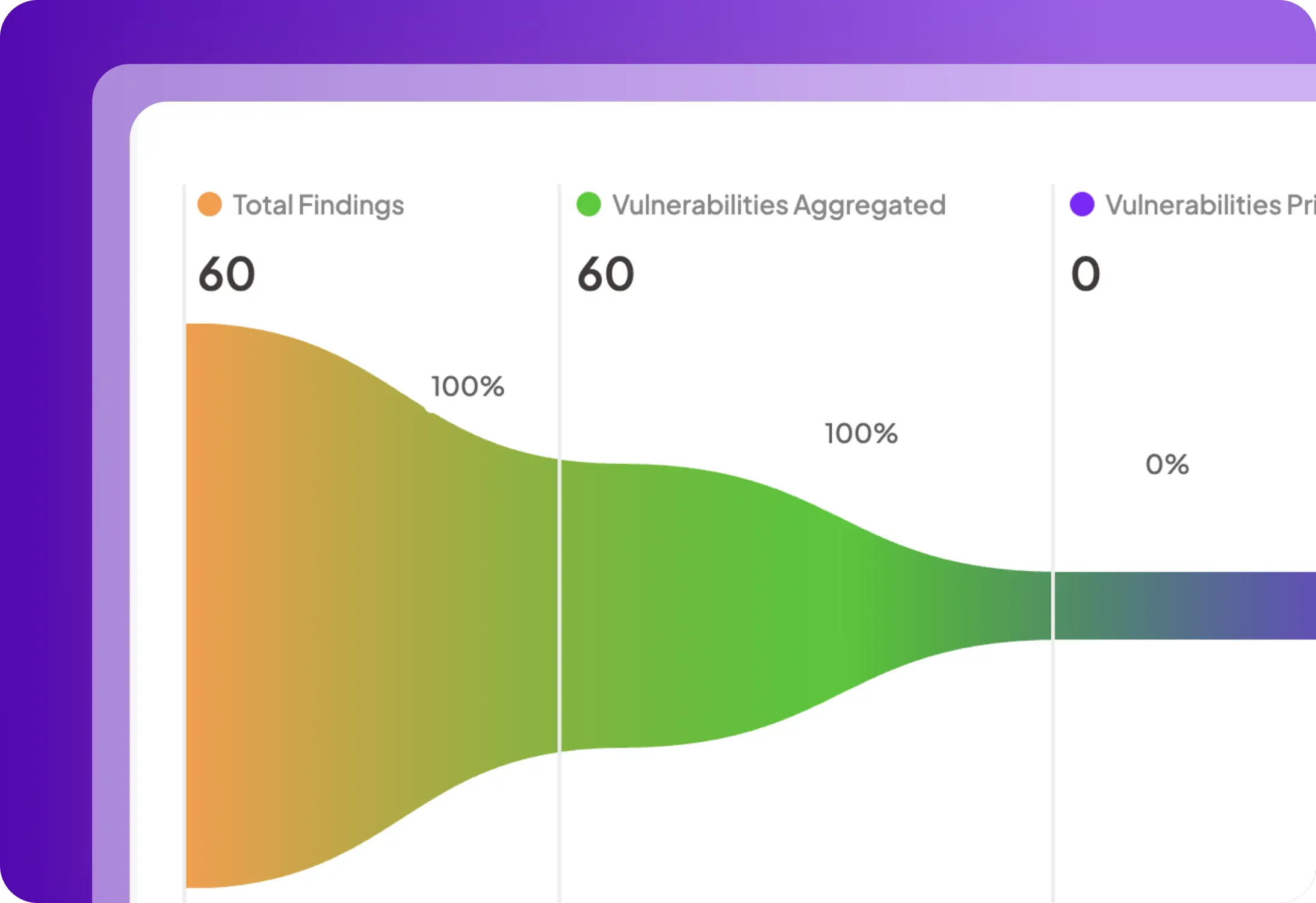
Scan Docker-containerafbeeldingen, detecteer CVE's, hardcoded geheimen en nalevingsrisico's in registries.
Plexicus containerbeveiliging scant afbeeldingen, handhaaft Kubernetes-beleid en blokkeert runtime-bedreigingen om workloads veilig en compliant te houden
Voorlopende teams zijn al binnen
















Bescherm container-applicaties van build tot runtime. Detecteer kwetsbaarheden, verkeerde configuraties en bedreigingen in realtime om veerkrachtige en conforme implementaties te garanderen.
Scan Docker-containerafbeeldingen, detecteer CVE's, hardcoded geheimen en nalevingsrisico's in registries.
Handhaaf RBAC, Pod Security Standards en netwerkbeleid automatisch.
Detecteer cryptojacking, privilege-escalatie en laterale beweging met automatische responsacties.
Genereer SBOM's, valideer licenties en onderteken containerafbeeldingen om uw toeleveringsketen te beveiligen.
Sluit Plexicus aan op GitLab, Jenkins of GitHub Actions voor containerbeveiligingsmonitoring tijdens ontwikkeling.
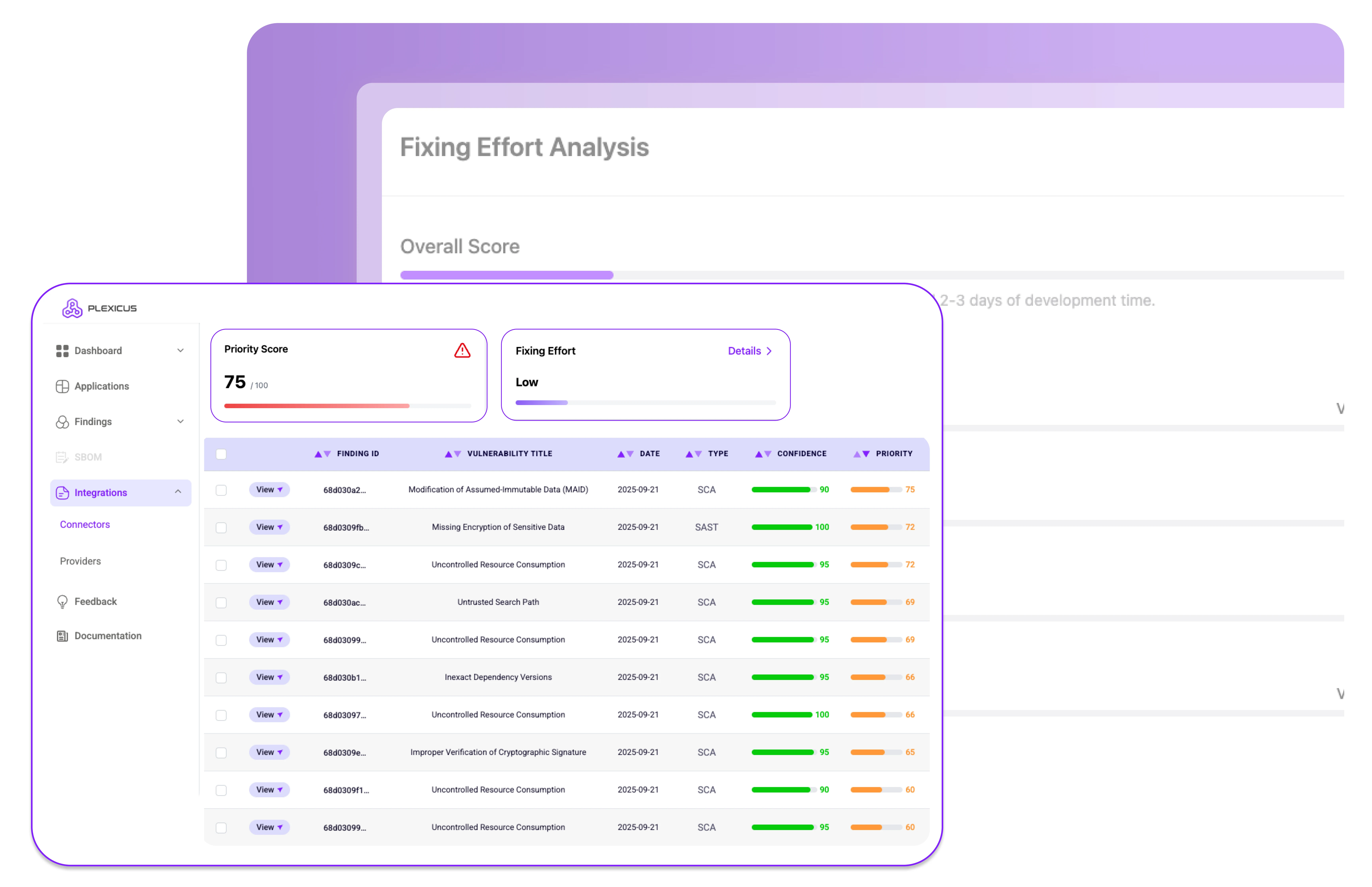
Uitgebreide beveiliging tijdens build, implementatie en runtime met realtime zichtbaarheid en verdediging.
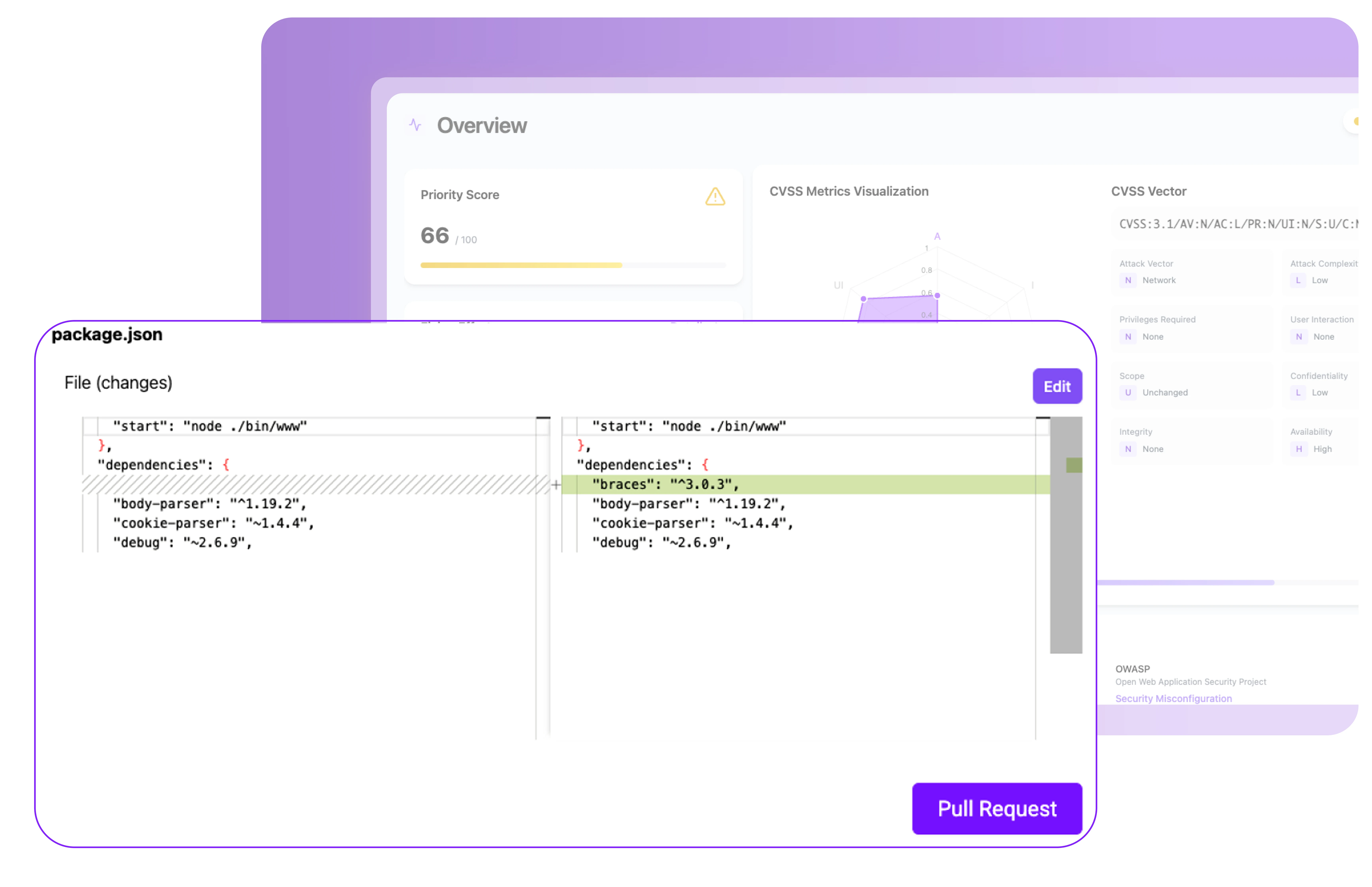
Scan containerafbeeldingen tijdens het buildproces om kwetsbaarheden in basisafbeeldingen, OS-pakketten en afhankelijkheden te ontdekken. Genereer een SBOM voor volledige zichtbaarheid en zorg ervoor dat problemen worden opgevangen voordat ze worden geïmplementeerd.
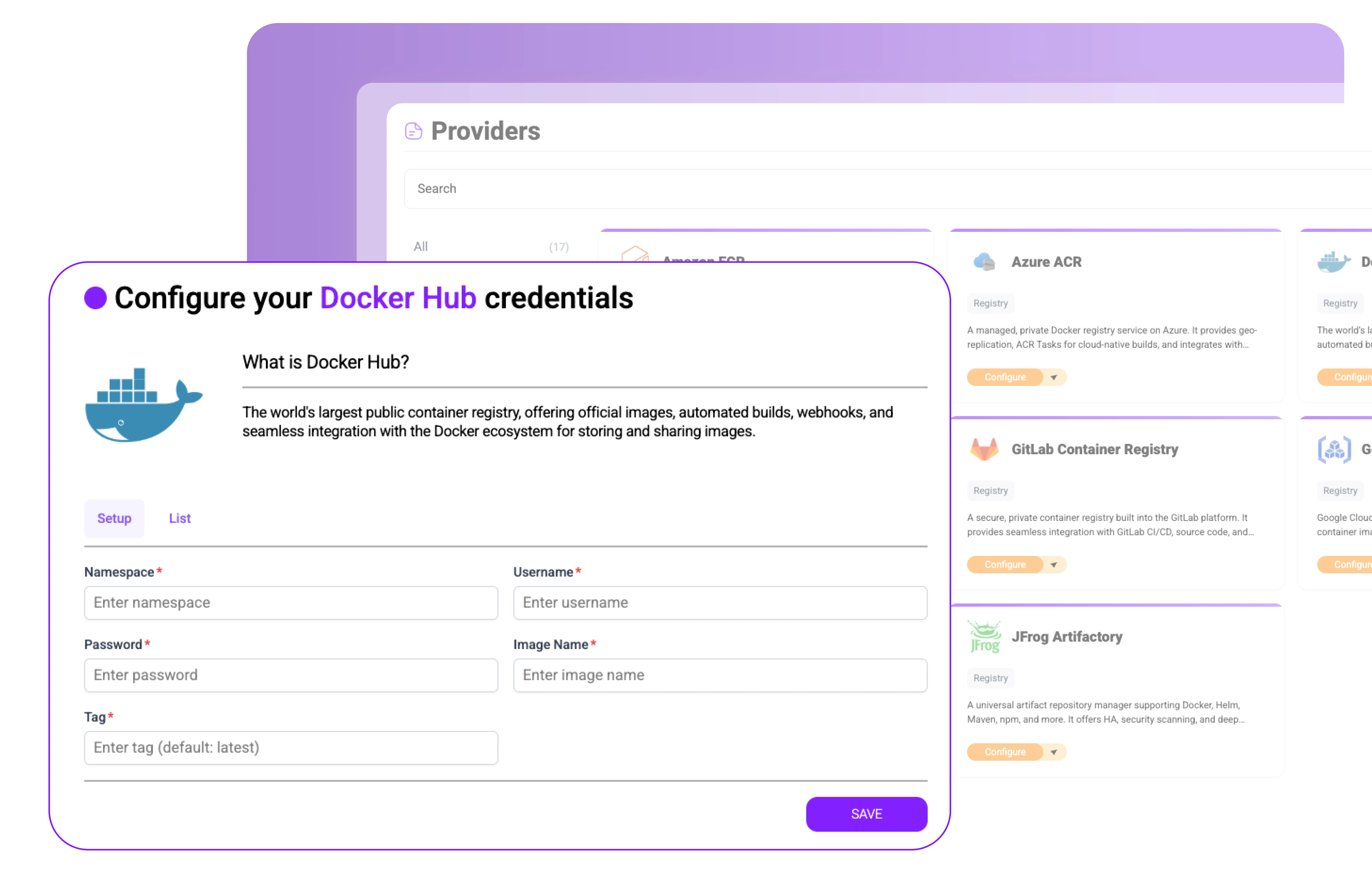
Integreer met registries zoals Docker Hub, AWS ECR, Azure ACR en GCR. Scan en onderteken automatisch afbeeldingen, detecteer geheimen of malware en handhaaf beleidsregels voordat containers ooit in productie worden gehaald.
Valideer Kubernetes-implementaties met CIS Benchmarks, Pod Security Standards en toelatingscontrolebeleid.
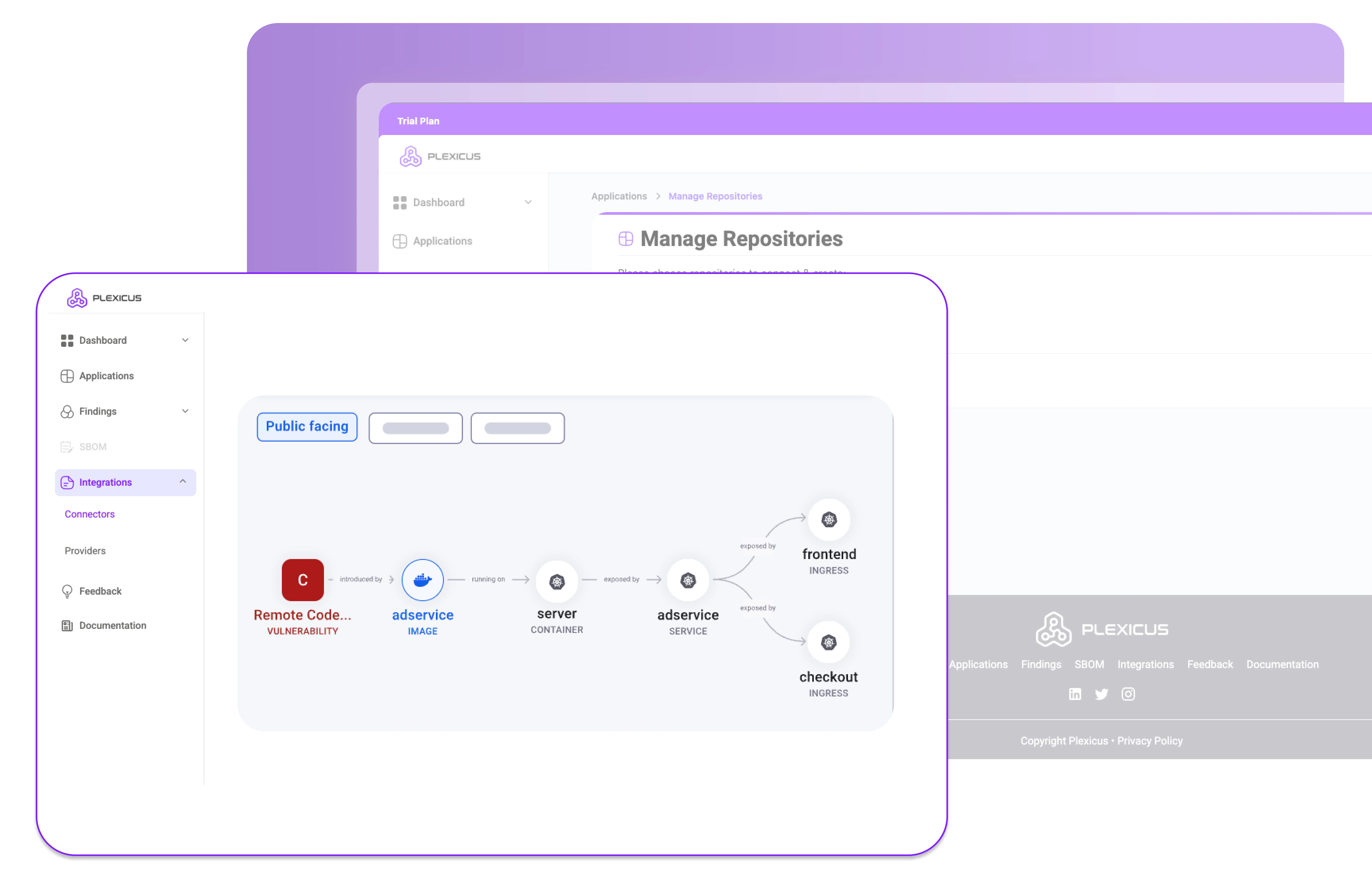
Monitor processen, netwerkactiviteit en bestandsintegriteit om containerbedreigingen in realtime te detecteren en te stoppen.
Verbind Plexicus Container Security met uw CI/CD-pijplijnen, registries en Kubernetes-omgevingen om containers te beveiligen zonder de ontwikkeling te vertragen
Plexicus maakt applicatiecontainerbeveiliging eenvoudig, van bouwen tot runtime.
Installeer Plexicus Container Security in registries & clusters
Vang kwetsbaarheden en verkeerde configuraties vroegtijdig op.
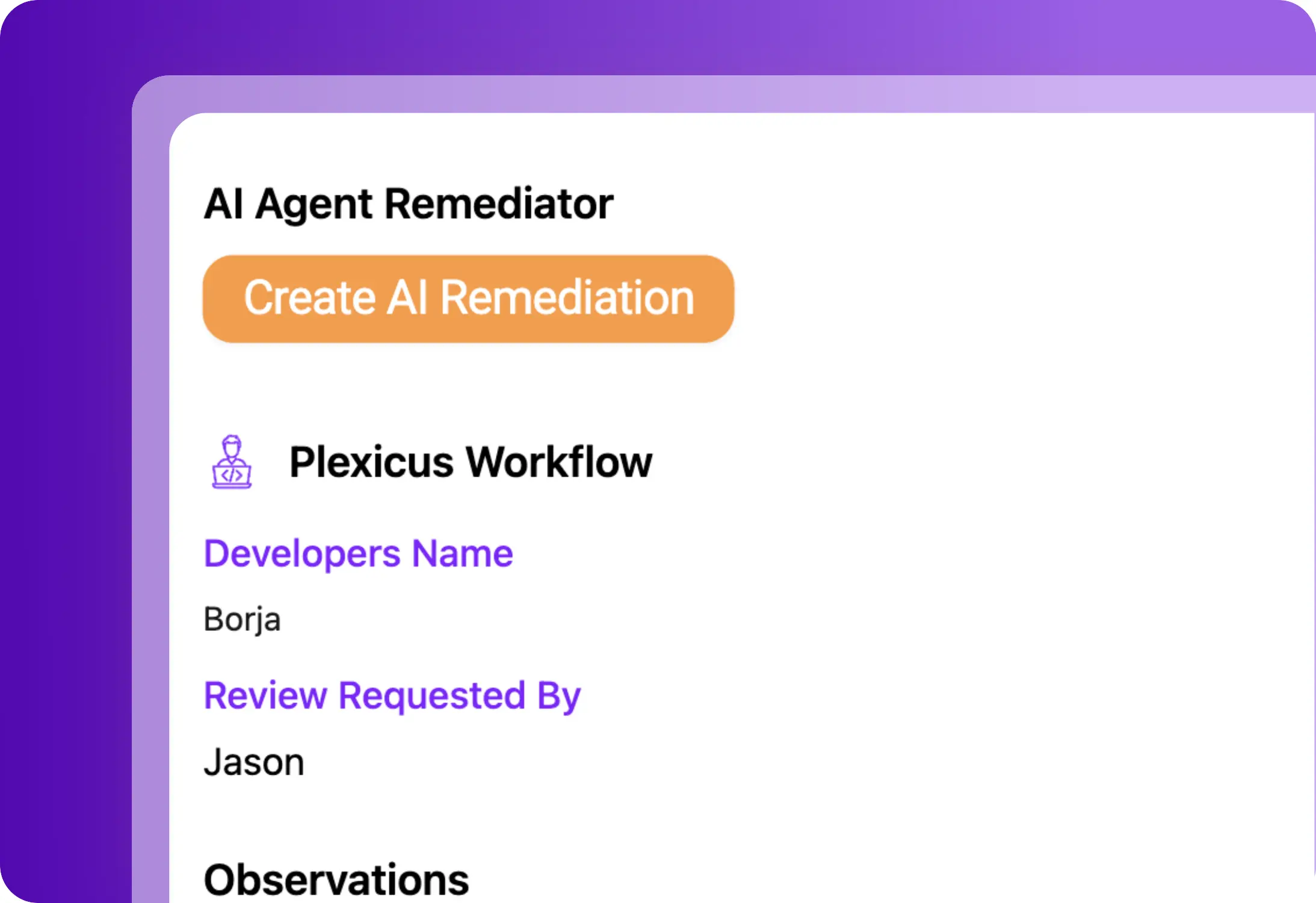
Blokkeer runtime bedreigingen voordat er schade is aangericht
Sluit je aan bij teams die Plexicus vertrouwen om de code die hun AI schrijft — en de code die ze erfden — te beveiligen.
As pioneers in cloud security, we've found Plexicus to be remarkably innovative in the vulnerability remediation space. The fact that they've integrated Prowler as one of their connectors demonstrates their commitment to leveraging the best open-source tools while adding significant value through their AI-powered remediation capabilities.

The AI agent's ability to automatically generate fixes for vulnerabilities has transformed our workflow.

As one of Plexicus's first customers, we've witnessed firsthand how their platform has evolved into an indispensable security solution. Their AI-powered remediation has dramatically reduced our vulnerability management overhead and allowed our security team to focus on strategic initiatives instead of repetitive fixes.

Plexicus's powerful vulnerability management allows us at Puffin Security to deliver more advanced cybersecurity services to our clients, creating a perfect security partnership.

Plexicus has revolutionized our remediation process - our team is saving hours every week!

The integration is seamless, and the AI-powered auto-remediation is a game-changer.

Plexicus has become an essential part of our security toolkit. It's like having an expert security engineer available 24/7.

Since implementing Plexicus, we've seen a dramatic improvement in our security posture with minimal effort from our team. The AI-driven approach to vulnerability remediation is truly revolutionary.

As pioneers in cloud security, we've found Plexicus to be remarkably innovative in the vulnerability remediation space. The fact that they've integrated Prowler as one of their connectors demonstrates their commitment to leveraging the best open-source tools while adding significant value through their AI-powered remediation capabilities.

The AI agent's ability to automatically generate fixes for vulnerabilities has transformed our workflow.

As one of Plexicus's first customers, we've witnessed firsthand how their platform has evolved into an indispensable security solution. Their AI-powered remediation has dramatically reduced our vulnerability management overhead and allowed our security team to focus on strategic initiatives instead of repetitive fixes.

Plexicus's powerful vulnerability management allows us at Puffin Security to deliver more advanced cybersecurity services to our clients, creating a perfect security partnership.

Plexicus has revolutionized our remediation process - our team is saving hours every week!

The integration is seamless, and the AI-powered auto-remediation is a game-changer.

Plexicus has become an essential part of our security toolkit. It's like having an expert security engineer available 24/7.

Since implementing Plexicus, we've seen a dramatic improvement in our security posture with minimal effort from our team. The AI-driven approach to vulnerability remediation is truly revolutionary.


Stop met kiezen tussen AI-snelheid en security-schuld. Plexicus is het enige platform dat Vibe Coding Security en ASPM parallel draait — één workflow, elke codebase.